- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SSL Decryption
- LIVEcommunity
- Discussions
- General Topics
- SSL Decryption
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
SSL Decryption
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-10-2016 09:10 AM
We do SSL Decryption on our PA.
Recently we have been seeing a lot of sites that do not decrypt
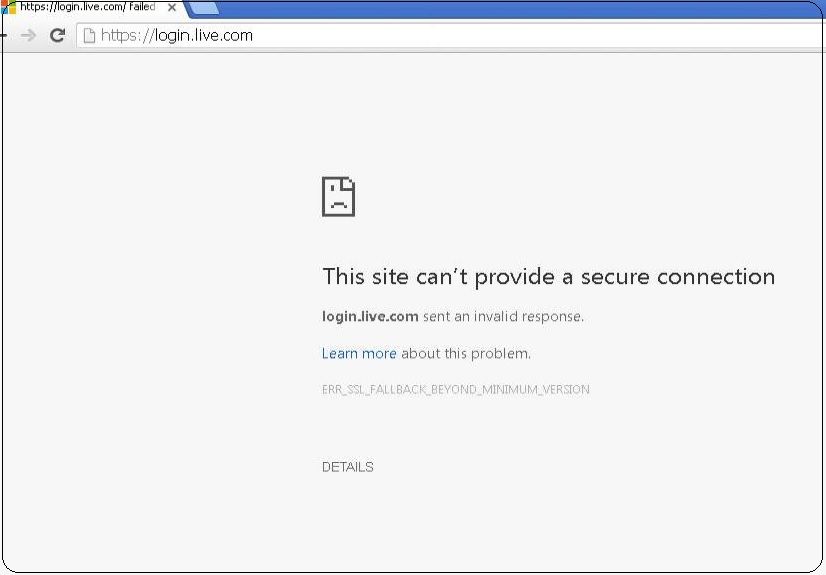
Chrome comes up with ERR_SSL_FALLBACK_BEYOND_
Firefox does not have any meaning full error message
A quick google shows that it is to do with disabling of SSL v3.
When the site is added to no decryption policy it works, so obviously the issue is to do with SSL Decryption
But I do not understand what is forcing the browser back to SSL v3.
Can anyone please point me in the right direction. Is it the SSL cert that is installed on the PA ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-10-2016 11:20 AM
If I had to guess, you're probably running PAN-OS 7.0 or older, so the list of ciphers supported by the decryption is limited to lower security ciphers (nothing using DHE or EC). If I'm wrong about the OS version, you can discard the rest of this message because I have no idea other than that.
If the site you're going to only supports high-encryption ciphers within TLS 1.0 and greater, the only option left to the firewall's decryption mechanism is to use SSLv3. Since SSLv3 is pretty much not supported by most current browsers unless you force it the error you see will happen (it can't negotiate any ciphers that it has in TLS, and the downgrade to SSLv3 fails).
PAN-OS 7.1 introduces a huge amount of additional ciphers within SSL forward decryption. If you are unable to upgrade to 7.1 yet, the only options would be to block the site or exclude it from your decryption policy.
Best regards,
Greg Wesson
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-11-2016 01:32 AM
Hi
I had a feeling it might be do with the PANOS , we run 6.1.x.
I have been holding off upgrading to 7.x since there were a lot of discussion on this forum about SSL Decryption bugs related to the PAN OS 7
Anyone else running PAN OS 6.x having these issues.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-11-2016 02:19 AM - edited 05-11-2016 02:29 AM
We have the same issue (PAN-OS 6.1.7)
Problem statrted in the last few days, after Chrome got an update to a new version: 50.0.2661.94
I tried to create a new certificate but it didn't solve the problem.
I understand that the only way to address this issue is to upgrade to 7.1.* ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-11-2016 06:27 AM
@RC-BHF as @gwesson stated it's because the PAN-OS version you're running doesn't support the cipher the website is using.
Further compounding the problem I know PAN-OS 6.X.X had a bug where allowing "unsupported ciphers" didn't matter:
(Screen shot is of 7.0.X - So formatting may be a bit off for you)
In theory you should be able to have this unchecked and the session should be allowed, but that isn't the case and the only way out is 1 of 3 options.
Turn off SSL Interception completely
Handle URLs on a case by case basis
Upgrade to 7.1.X (as 7.1.X has the huge bump in cipher support)
Back when i was running 7.0.3 we were still running into issues where unsupported ciphers still needed to be bypassed eventhough our decryption profile is built to avoid this issue.
The TAC case I had at the time the support tech said, while it *SHOULD* not be a problem they couldn't gurantee it wouldn't cause the problem.
Since we've been running 7.0.5-h2 I haven't had a single case where an unsupported cipher site needed to be bypassed. So maybe that issue has been solved.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2016 08:19 AM
Just a quick update - we solved the problem by upgrading to 7.0.6.
- 4583 Views
- 5 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- Foward Trust Cert and MacBook Pro in General Topics
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions