- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPN site-2-site configuration and OSPF
- LIVEcommunity
- Discussions
- General Topics
- Re: VPN site-2-site configuration and OSPF
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
VPN site-2-site configuration and OSPF
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-07-2019 07:04 AM
Hello forum members,
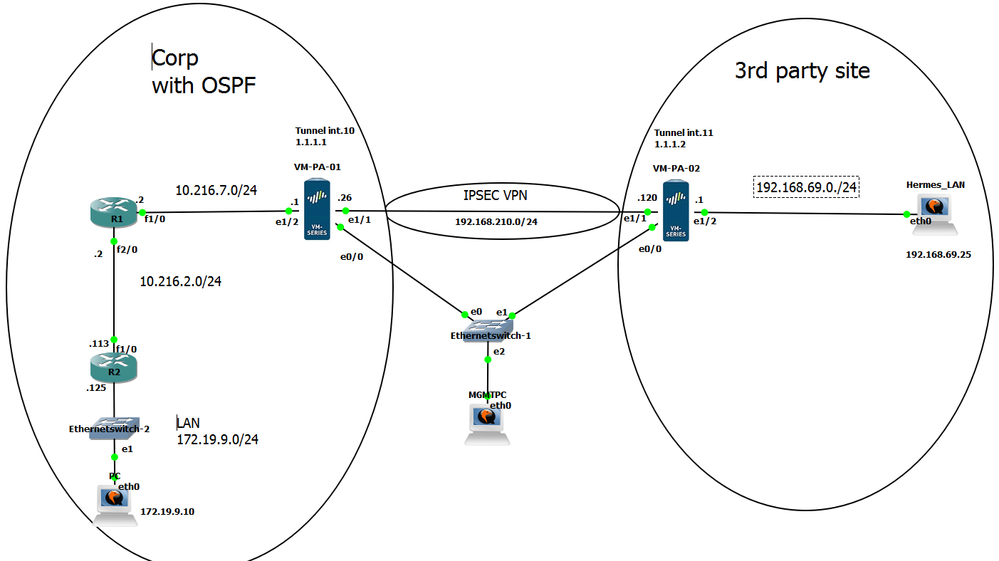
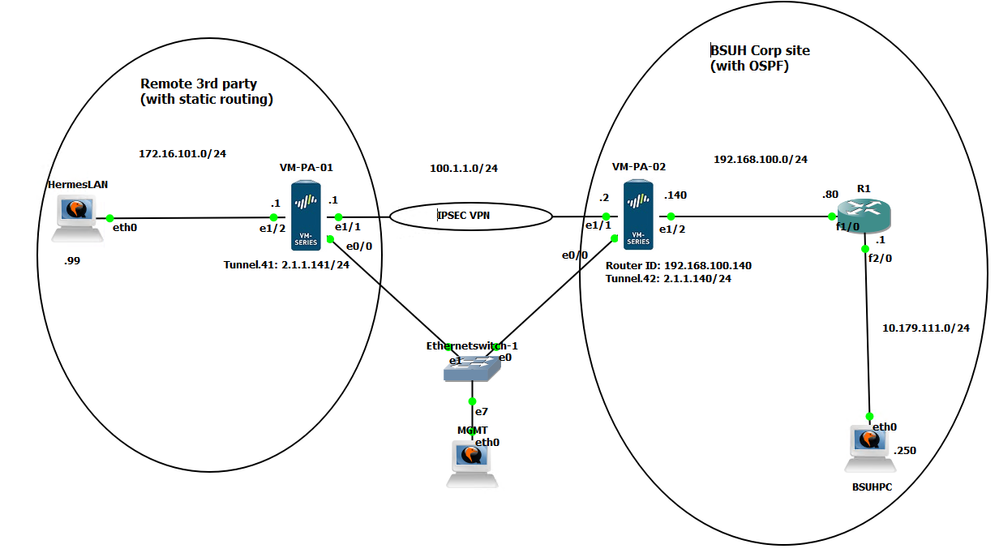
I have been testing the VPN site-2-site configurations on my Palo Alto VM lab, prior to deploying on our production environment. I have successfully set up a VPN connection where both firewalls use static routing. Trouble I'm having now is setting up the VPN connection where the 3rd party site uses static routing and my corp LAN uses OSPF.
I can't get the tunnel up between the two sites. I followed the Site-2-Site VPN with Static and Dynamic Routing example in the PAN-OS Admin guide, but some of the steps seem vague (vague to me any way). My R1 router has formed an OSPF neighbour relation ship with the Palo Alto VM-PA-01 fine and the PC host 172.19.9.10 can ping the E1/2 interface (10.216.7.1) of the Palo Alto fine.
The following is my lab topology and screen shots of the configs.
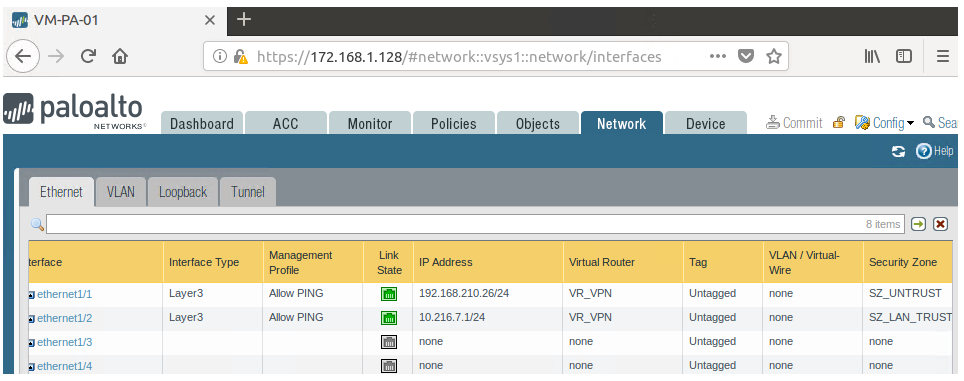
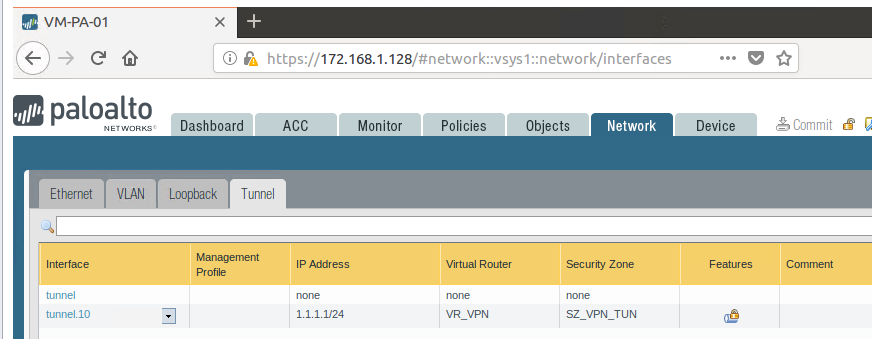
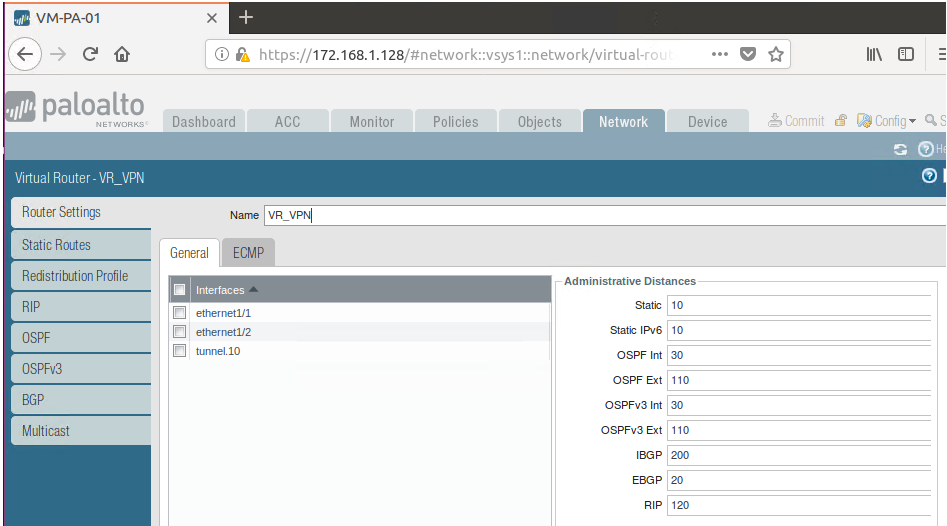
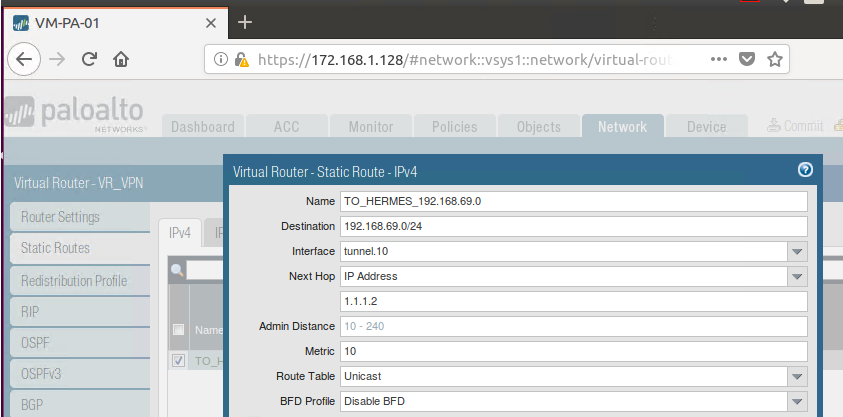
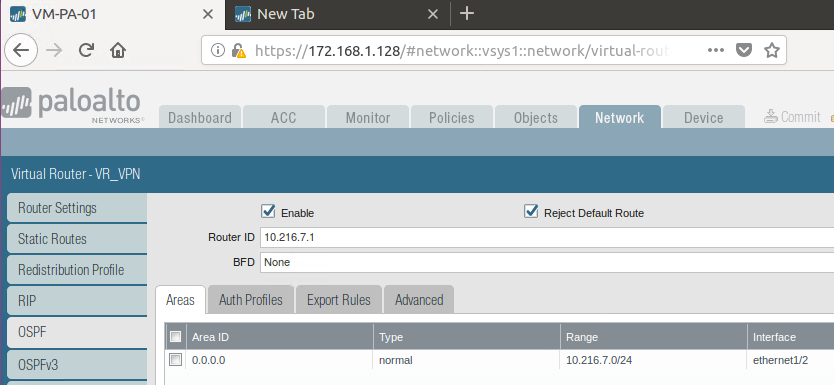
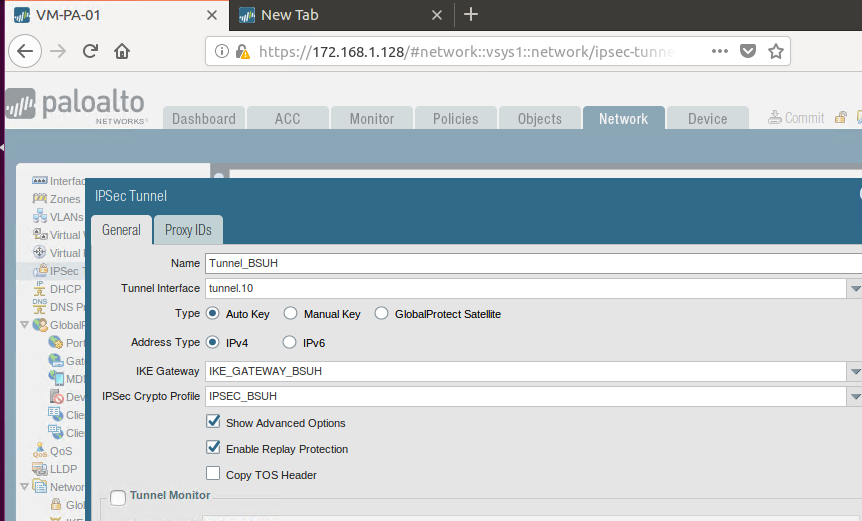
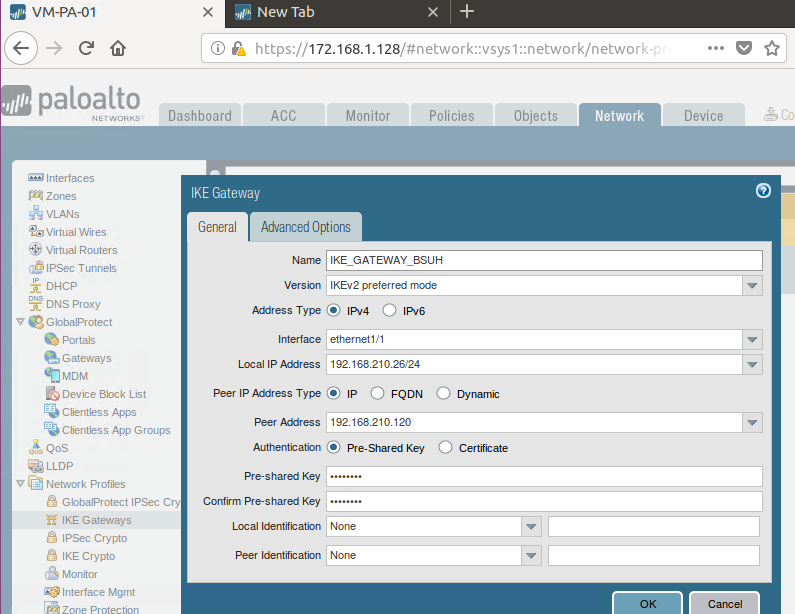
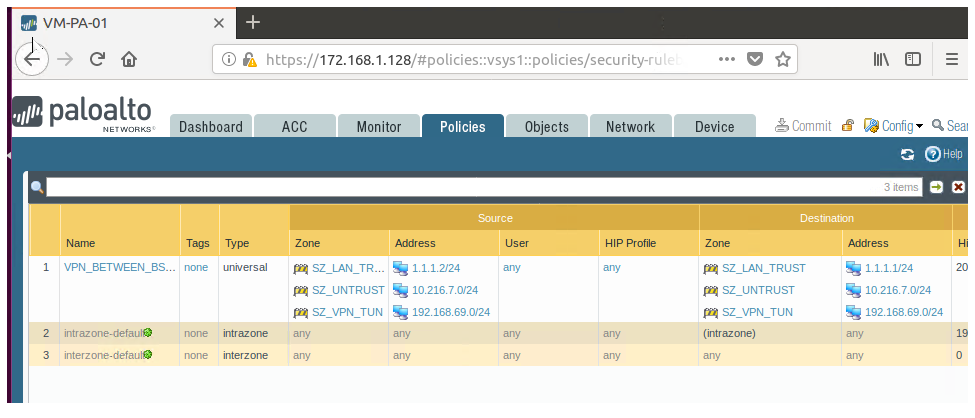
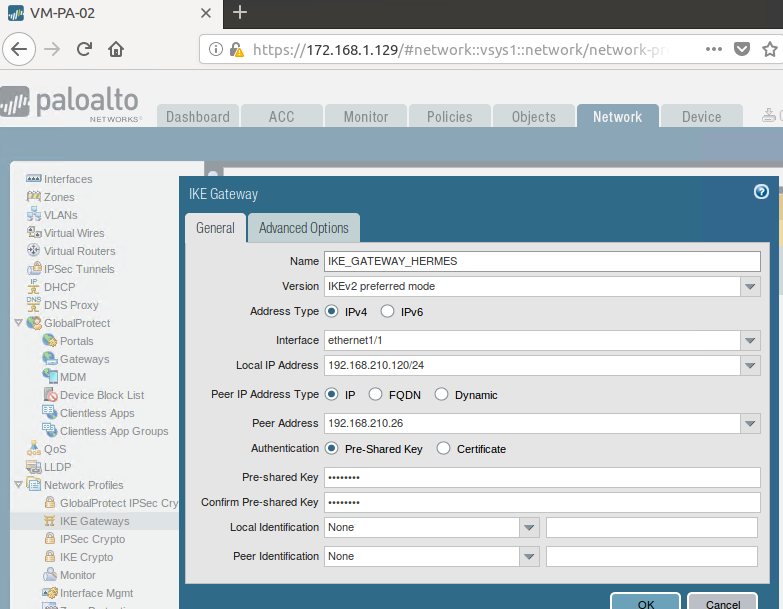
VM-PA-01 config.
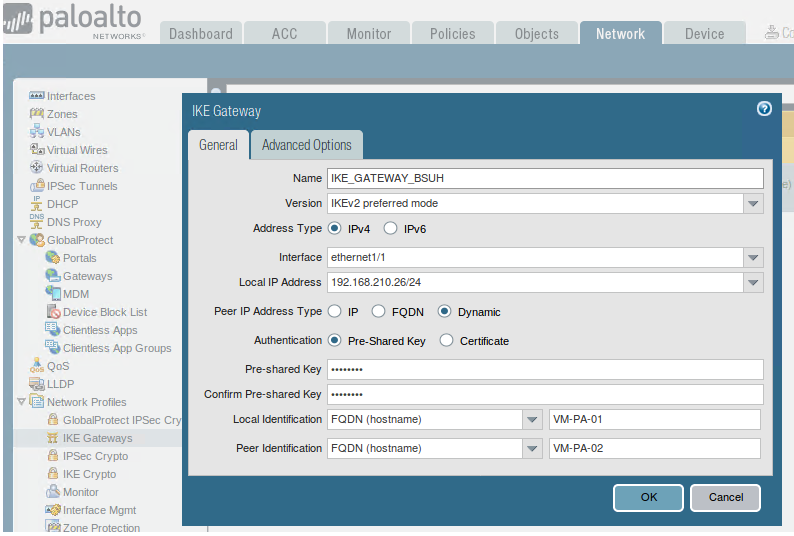
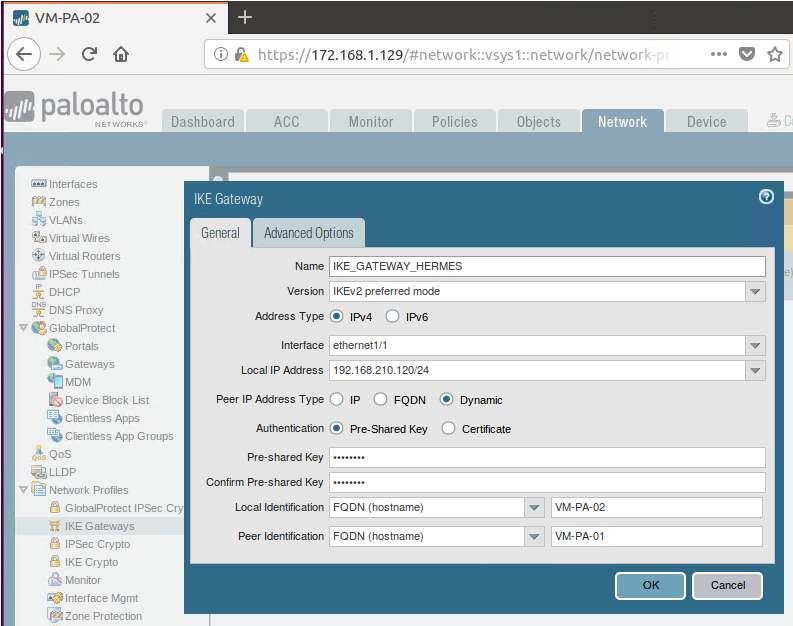
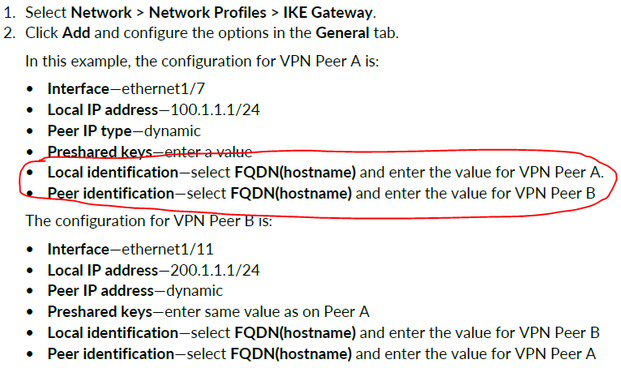
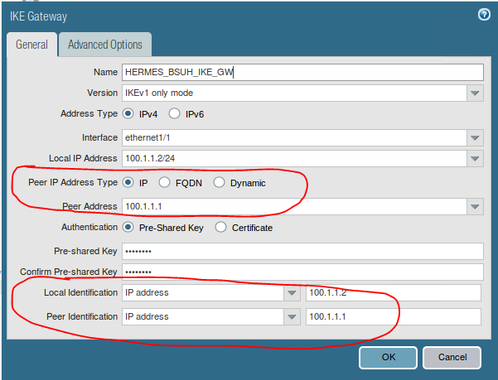
*** I also tried this IKE Gateway config with the FQDNs, as in the PAN-OS guide ***
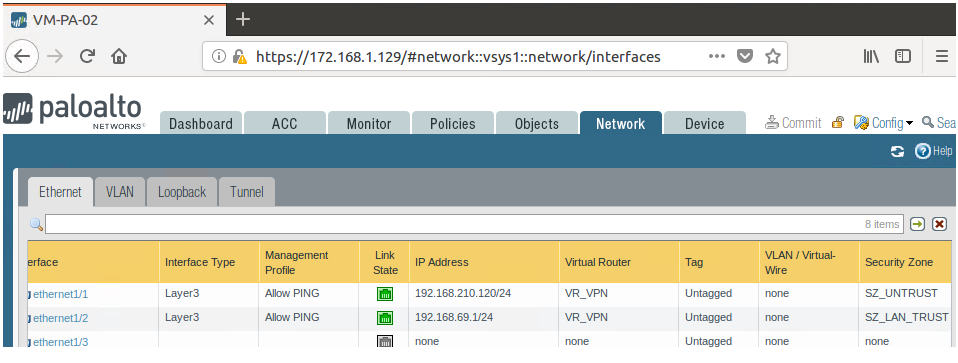
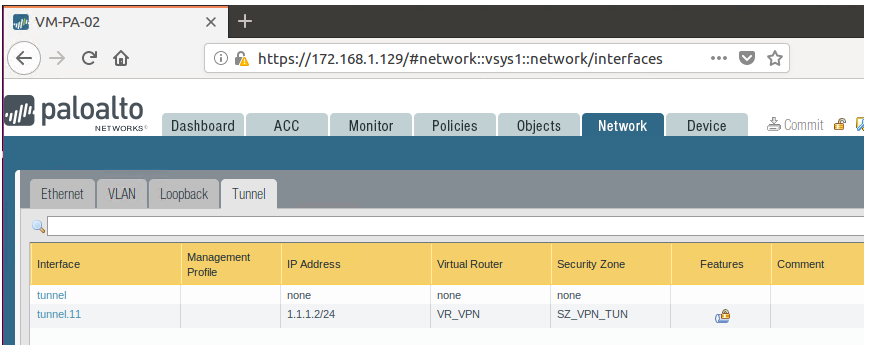
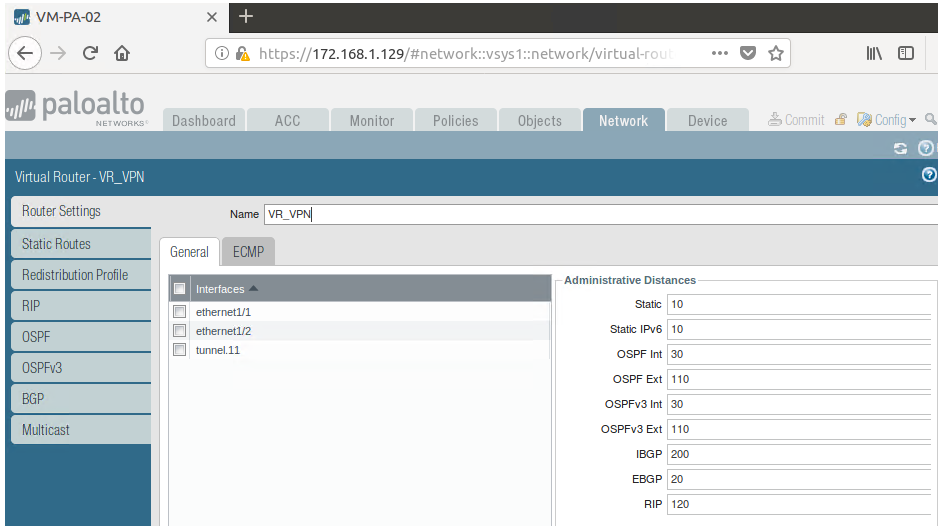
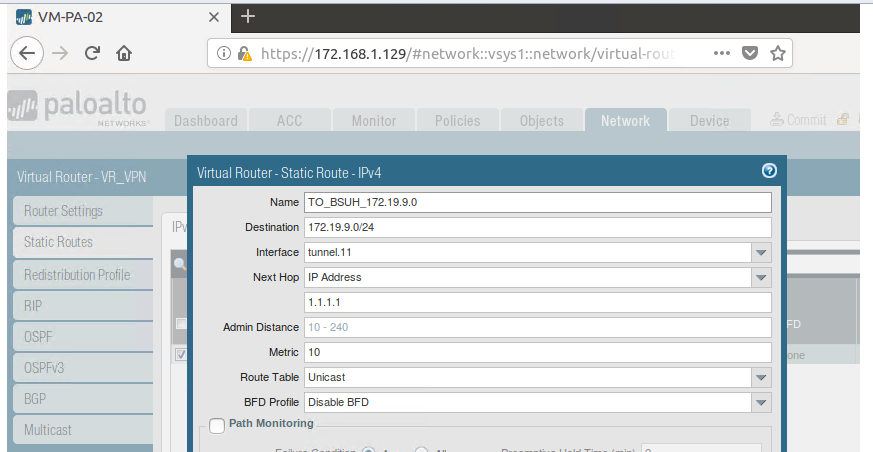
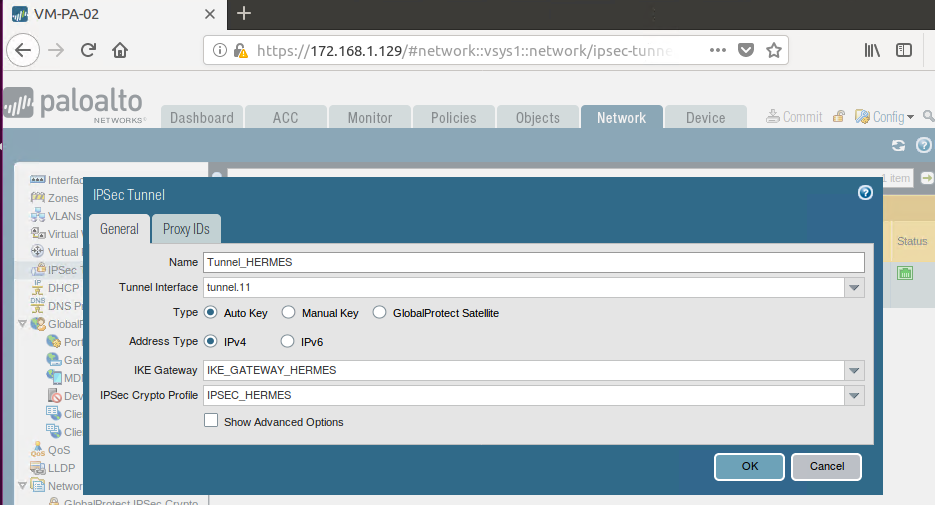
VM-PA-02 config.
*** I also tried this IKE Gateway config with the FQDNs, as in the PAN-OS guide ***
Any suggestions and advice will be much appreciated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-07-2019 08:52 AM
Hello,
I took a bit of a look, and I didnt see a route between the PAN's? Can the external interfaces of the two ping each other? You will have to add a monitoring profile to it so they can reply as well as a security policy. What I do is always have a static route between the two for monitoring, but they need to be able to see each other.
Just a thought.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-07-2019 05:22 PM
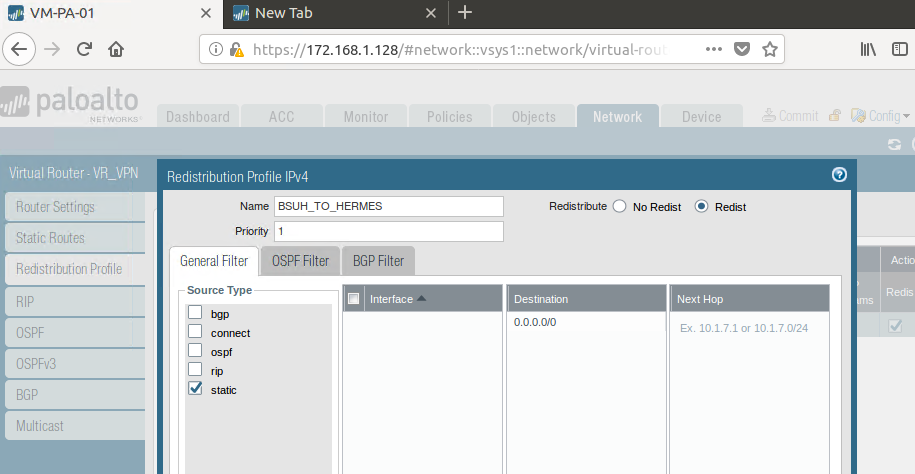
In the OSPF configuration, do you have the redistribution rule setup to pull in the static route pointed to the remote site vpn and distribute it down to your "corp" lan for the return path.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2019 02:22 AM
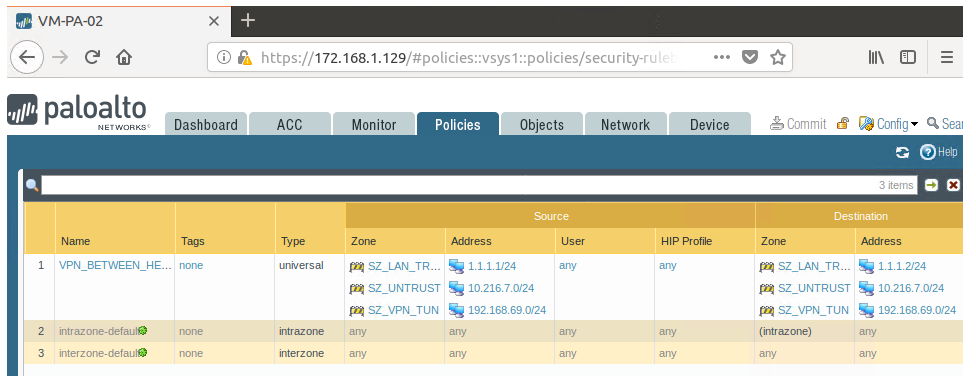
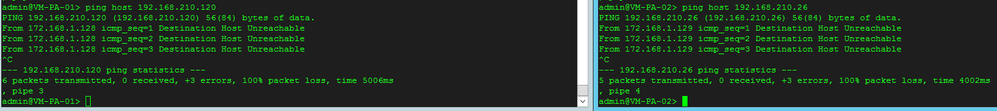
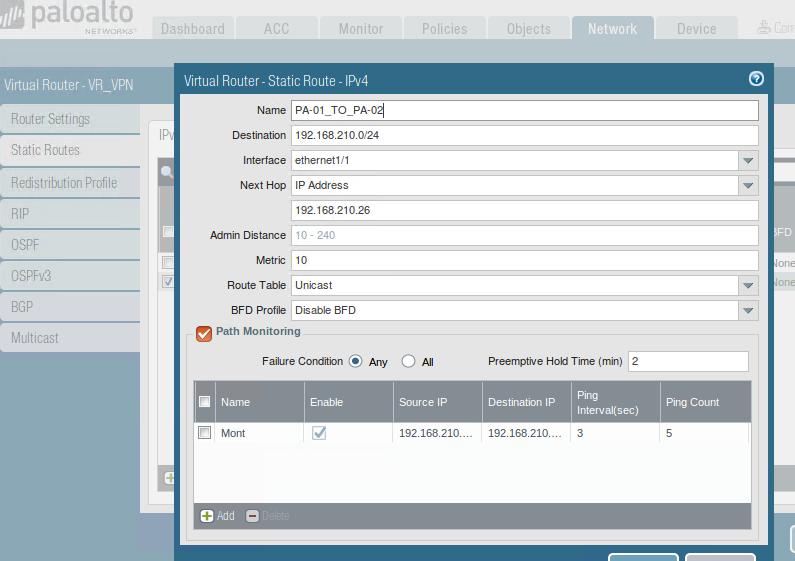
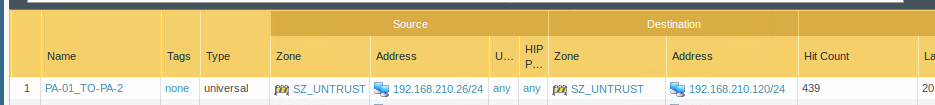
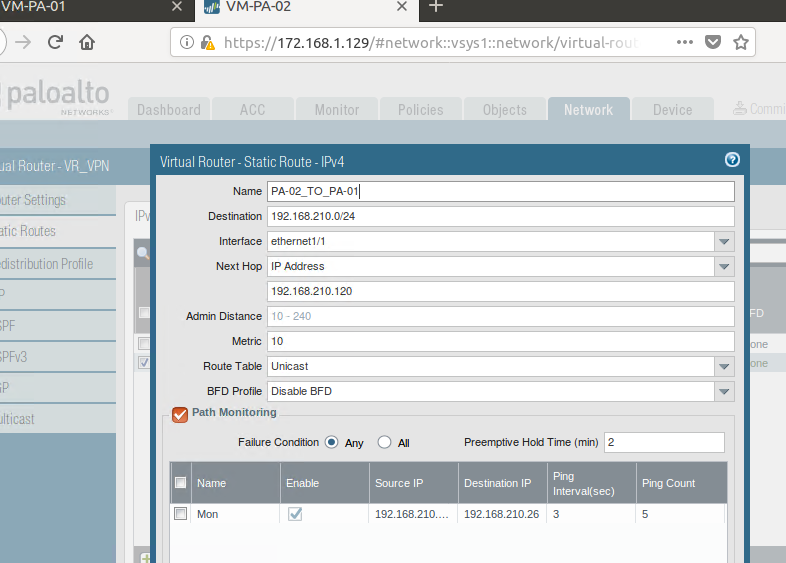
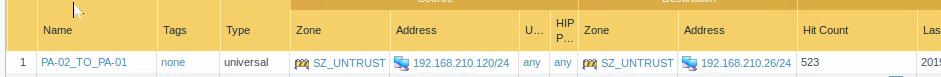
Thank you for your reply. I can't ping between the two Palo's on IPs 192.168.210.26 and 192.168.210.120, which are assigned to their e1/1 interfaces. I have set up statics routes anda security policy as follows on both Palo's as suggested.
VM-PA-01 config.
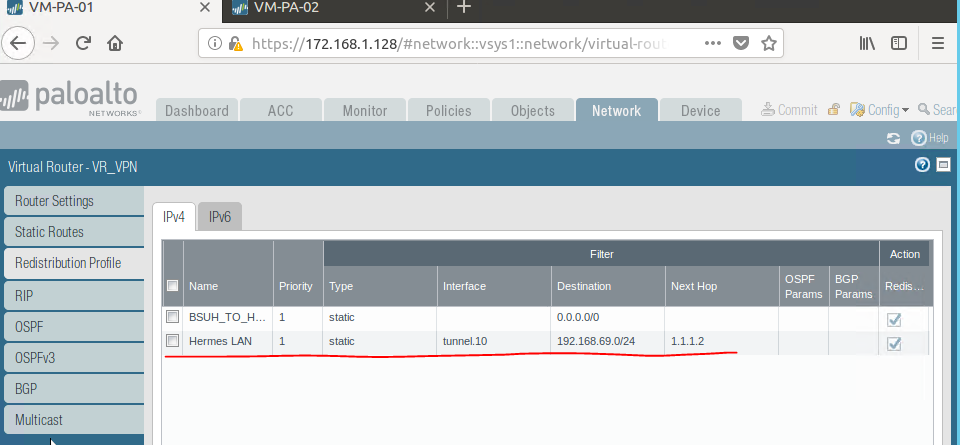
VM-PA-02 config.
Any further advice is appreciated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2019 07:13 AM
Hello,
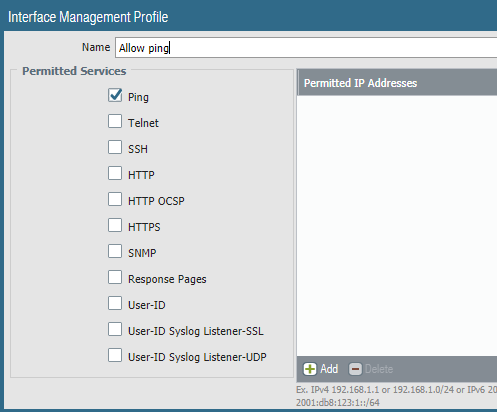
Make sure you have set an Interface Management Profile and at least allow ping on both PAN's. It looked like your security profile would already allow ping.
Keep an eye on the logs to see what is getting blocked if anything.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2019 07:17 AM
Hello,
I just noticed you didnt source your pings so they would have come from the maangement interface. Try the following:
From VM-PA-01
Ping source 192.168.210.26 host 192.168.210.120
From VM-PA-02
Ping source 192.168.210.120 host 192.168.210.26
See if that returns any good replies. But the fact that the pings stated 'Destination Host unreachable' tells me that routing could be an issues from your management interface.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-08-2019 02:56 PM
Have you assigned the underlined redistribution profile to an export rule in OSPF?
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2019 05:04 AM
As rmfalconer notes, you also need to assign the redistribution profile to OSPF for it to become active. Without both steps the local static route will not be redistributed to the rest of the OSPF infrastructure for the return path.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-11-2019 04:58 AM
Hi pulukas, rmfalconer, Otakar.Klier,
Thank you for your responses and advice.
@OtakarKlier- Both the Palo's can ping each other if I source the IPs, even when I don't have static rule set up
I lab'd this up again following the Site-to-Site VPN with Static and Dynamic Routing config guide in the PAN-OS 8.1 Admin guide and got the tunnels up with the remote sites pinging each other.
However, it did take a bit of tweaking with trial and errors, until I got the config working. The config steps are not clear in the Admin guide, if one is new to Palo Alto and VPNs.
These are the observations I made when I lab'd this up again.
1. On the IKE Gateway configuration, the Admin. guide said use the FQDN for the local and peer identification. This did not work for me in my lab.
Instead, I used the following config on both Palo's, by specifying the Peer IP address and the local and the IP peer addresses for the Local and Peer identification:
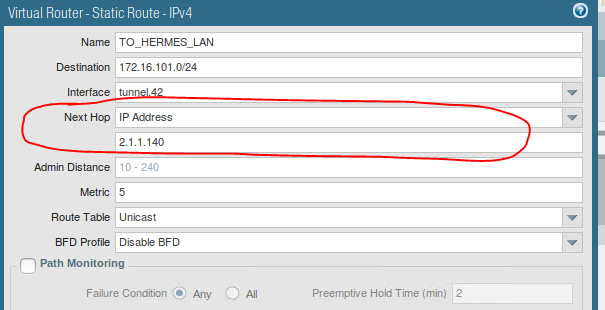
2. I was told that static routes pointing down tunnels should not have a next hop address defined. If it did not, how would the secure traffic travel across the tunnel? in order for my config to work, i had to specify the Next Hop IP address of the tunnel interface.
3. Both my Palo Alto's do not see each other as OSPF neighbours. Surely they would only see each other as OSPF neighbours, if both Palo's had OSPF running on them? Not sure why the guide stated this, only one of the Palo's has OSPF configured. The peer VM-PA-02 which has OSPF configured. has formed a neighbour relationship with router R1 fine.
Anyone else had to tweak things to their configs working?
Many thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-11-2019 01:47 PM
Glad you got it working!
- 9254 Views
- 10 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- BFP with OSPF graceful restart causing outages during failover in Next-Generation Firewall Discussions
- Backup Internet with Ipsec VPN doing BGP in General Topics
- OSPF route suppression in General Topics
- How to configure GRE over Ipsec in Next-Generation Firewall Discussions