- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Announcing VM-Series Integration with Google Cloud Network Connectivity Center
- LIVEcommunity
- Articles
- General Articles
- Announcing VM-Series Integration with Google Cloud Network Connectivity Center
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 05-25-2021 06:16 AM - edited on 11-09-2022 12:02 PM by mmclimans
Introduction
Palo Alto Networks VM-Series Next-Generation Firewall for Google Cloud is the industry-leading virtualized firewall to protect applications and data with next-generation security features that deliver superior visibility, precise control, and threat prevention at the application level. The VM-Series capabilities to secure globally connected networks are further enhanced by its integration with Network Connectivity Center by Google Cloud.
How VM-Series + Network Connectivity Center Works
There are several components used to integrate the VM-Series with Network Connectivity Center.
Network Connectivity Center – Hubs and Spokes
Network Connectivity Center leverages a hub-and-spoke model to provide end-users a single place to manage global connectivity across various networks. The hub is a global resource that connects attached spokes with a simple and singular connectivity model. The Network Connectivity Center hub creates a full mesh networking model between the VM-Series and all other connected spokes. The VM-Series connects to the hub as a router appliance spoke.
Google Cloud Router
The VM-Series integrates with Network Connectivity Center by establishing BGP peering relationships with a VPC’s Cloud Router. This relationship enables full route propagation between remote networks and the Google Cloud VPC fabric routes.
Once the peering relationship is established between the Cloud Router and the VM-Series, routes from remote networks, Google Cloud VPCs, and the VM-Series are exchanged. If the VM-Series firewalls are deployed within the same spoke, the hub advertises the same prefixes to all of the firewalls. This behavior enables equal-cost multipath (ECMP) for hub to firewall traffic. If you prefer to isolate traffic flows to dedicated firewalls, the VM-Series should be placed in separate spokes with different ASNs.
Example Topologies
The VM-Series can be used to secure traffic from remote networks to Google Cloud VPCs. The following outcomes are achieved through the integration with Network Connectivity Center:
- Secure remote traffic to Google Cloud with optimal route selection.
- Encryption for data in transit.
- Secure remote traffic for a global VPC network.
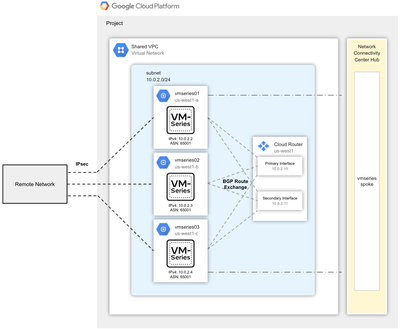
Topology 1: Regional VPC
In this topology, VM-Series firewalls are deployed across different zones within the same region. The firewalls are connected as a single spoke to the Network Connectivity Center hub and have a BGP session established with the VPC’s Cloud Router. From on-premises, IPsec tunnels are created and terminated on each firewall. Routes to and from the remote network and the VPC are exchanged through the VM-Series and Cloud Router. The VM-Series firewalls are advertising the same prefixes and MED values to take advantage of Google Cloud’s ECMP functionality. The use of ECMP provides redundancy and load distribution among the zonally distributed firewalls.
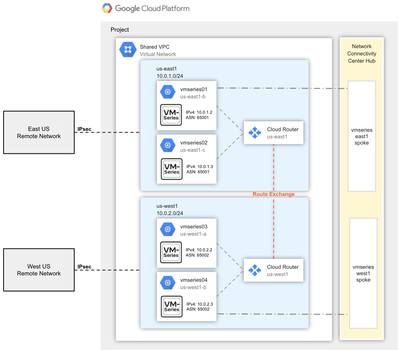
Topology 2: Global VPC
The architecture shows two VM-Series pairs (within the same VPC) distributed across two Google Cloud regions. Each firewall pair is a separate spoke connected to the Network Connectivity Center hub. The Cloud Router BGP peers with its respective regional firewall pair. Routes from the remote sites are advertised to the VM-Series firewalls via the Cloud Router. The Cloud Routers themselves exchange routes to provide full mesh connectivity.
Additional Resources
Nice addition gives a lot of flexibility in GCP,
I have a customer who I have helped deploying firewalls behind GCP iLB (internal LB) and set the next hop to the iLB. They are using Interconnect (Dedicated) no the IPsec tunnel for accessing on-prem.
Would you consider another topology where iLB as the next-hop is used as an extension of 1a and 2a as a supported method?
Unfortunately I wasn't able (anymore?) to edit the above comment.
However I managed to setup the BGP peering, but GCP won't redistribute imported VPC peering routes automatically.
Is this something that can be changed, without the need to add them as custom routes to the redistribute profile of the cloud router ?
In this solution, can the Palos be ran as a HA cluster and they share session info?
E.g.
Outbound Traffic: Onprem-server1 -> Palo1 -> Cloud-Server1
Reply traffic: Cloud-server1 -> Palo2 -> Onprem-server1
Thanks,
Aidan.
- 27225 Views
- 4 comments
- 4 Likes
-
"Address Objects"
1 -
10.0
2 -
10.1
2 -
10.2
3 -
8.1
1 -
9.0
1 -
9.1
1 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
Alibaba
2 -
Alibaba Cloud
3 -
Ansible
1 -
antivirus
1 -
API
2 -
applications
2 -
APS
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
3 -
AWS
6 -
Azure
1 -
Basic Configuration
4 -
Beacon
2 -
Beacon2020
1 -
Best Practices
4 -
Block List
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CLI
4 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
Cloud NGFW
1 -
Cloud Security
1 -
Collector Group
1 -
Commit Process
1 -
community news
1 -
Configuration
9 -
Configuration and Management
2 -
Configure Next Generation Firewall
1 -
console
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
5 -
COVID-19
1 -
CPSP
1 -
cyber elite
1 -
Cyberelite
11 -
dag
2 -
Debug
1 -
debugging
2 -
Default Policy
1 -
Deployment
1 -
discussions
1 -
EDL
3 -
education
2 -
Education and Training
2 -
Education Services
2 -
Educational Services
1 -
Effective Routing
1 -
Endpoint
1 -
ESXi
1 -
Events
1 -
Expedition
1 -
export
1 -
failover
1 -
FAQ
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
2 -
Focused Services Proactive Insights
1 -
gateway
1 -
Gateway Load Balancer
3 -
Gateway Loadbalancer
2 -
GCP
5 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
8 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
3 -
google cloud platform
4 -
GWLB
3 -
Hardware
2 -
hash
1 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
2 -
IoT Security
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
2 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
1 -
Log Collector Design
1 -
Log Forwarding
1 -
Log4Shell
1 -
Logging
2 -
login
1 -
Logs
3 -
Malware
1 -
Management
8 -
Management & Administration
5 -
MFA
1 -
microsoft
2 -
Microsoft 365
1 -
Migration
1 -
minemeld
24 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NetSec
1 -
NetSec Newsletter
1 -
network security
37 -
network-security
1 -
Networking
1 -
New Apps
1 -
News
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
4 -
ngfw
27 -
NGFW Configuration
10 -
NGFW Newsletter
1 -
Objects
2 -
Oracle Cloud
1 -
Oracle Cloud Infrastructure
1 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS 9.1
1 -
Panorama
10 -
Panorama 8.1
1 -
Panorama 9.1
1 -
Panorama Configuration
2 -
Panorama HA
1 -
PBF
1 -
PCNSA
2 -
PCNSE
2 -
performance
1 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma
1 -
prisma access
5 -
Prisma SD-WAN
1 -
proactive insights
2 -
QRadar
1 -
Radius
1 -
Ransomware
1 -
region
1 -
Registration
1 -
Release Notes
1 -
reporting and logging
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
2 -
script
2 -
SD WAN
1 -
SD-WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Session Packet
1 -
Setup & Administration
7 -
Site-to-Site VPN
1 -
Split Tunneling
1 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Logging Service
2 -
Support Guidance
1 -
syslog
1 -
Tag
2 -
Tags
2 -
Terraform
2 -
TGW
3 -
threat log
1 -
Threat Prevention
2 -
Threat Prevention License
1 -
Threat Prevention Services
1 -
Tips & Tricks
2 -
tls
1 -
traffic_log
1 -
Transit Gateway
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
troubleshooting
5 -
tunnel
2 -
Tutorial
2 -
Ubuntu 16.04
1 -
Unified Monitoring
1 -
Upgrade
2 -
upgrade-downgrade
3 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
15 -
VM-Series on AWS
7 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
2 -
VPNs
4 -
Vulnerability Protection
1 -
Webinar
1 -
WildFire
3 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2





