- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Firewall rules for palo alto to update the content (anti-virus,signature...
- LIVEcommunity
- Discussions
- General Topics
- Firewall rules for palo alto to update the content (anti-virus,signature...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-31-2020 11:24 PM
Hi, anyone can advise how to configure the firewall rule for palo alto to update its contents? Thanks in advance.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2021 07:37 AM
Nice, I'll give it a try with this filter.
Thanks for the recommendation!
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2020 04:07 AM
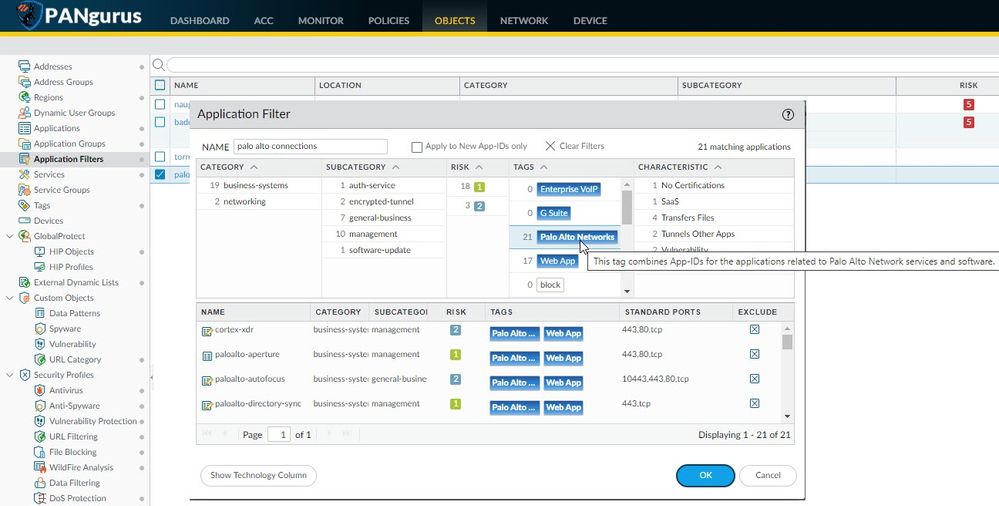
if you've upgraded to 9.1 or later, you can leverage the palo alto tag in an application filter to dynamically allow all connections needed by your firewalls.
using this filter in a security rule will allow outbound connections and if ever a new service is added, or an existing one is changed, the filter will account for these automatically
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2020 05:12 AM
Thanks for the reply @reaper . But not only for application update, also for other update (anti-virus, IPS...). Out PA the management interface is connected to internal network , so how should create a firewall rule for PA update? I tried to create a rule to let management subnet outgoing traffic, but when click downloading under Dynamic update , it still shows failed. Can you please what firewall rules need for palo alto update? thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2020 05:25 AM
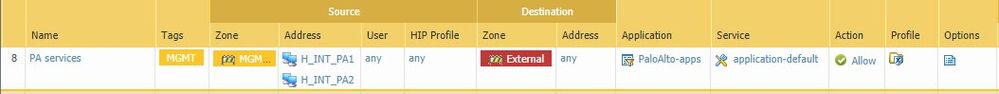
All of the services and updates are included in that application filter, the only exception is when your firewall is not using your internal DNS and needs to reach out to an internet DNS, in which case you need to also allow outbound DNS, and possibly ntp and ping to sync time and troubleshoot
if you do not have access to the application filter TAG, you will need the following applications for basic services, more may be required depending on your deployment)
- paloalto-dns-security
- paloalto-updates
- paloalto-wildfire-cloud
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2020 05:29 AM
Thanks @reaper . PA will use management IP or external IP address to download the updates?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-01-2020 05:37 AM
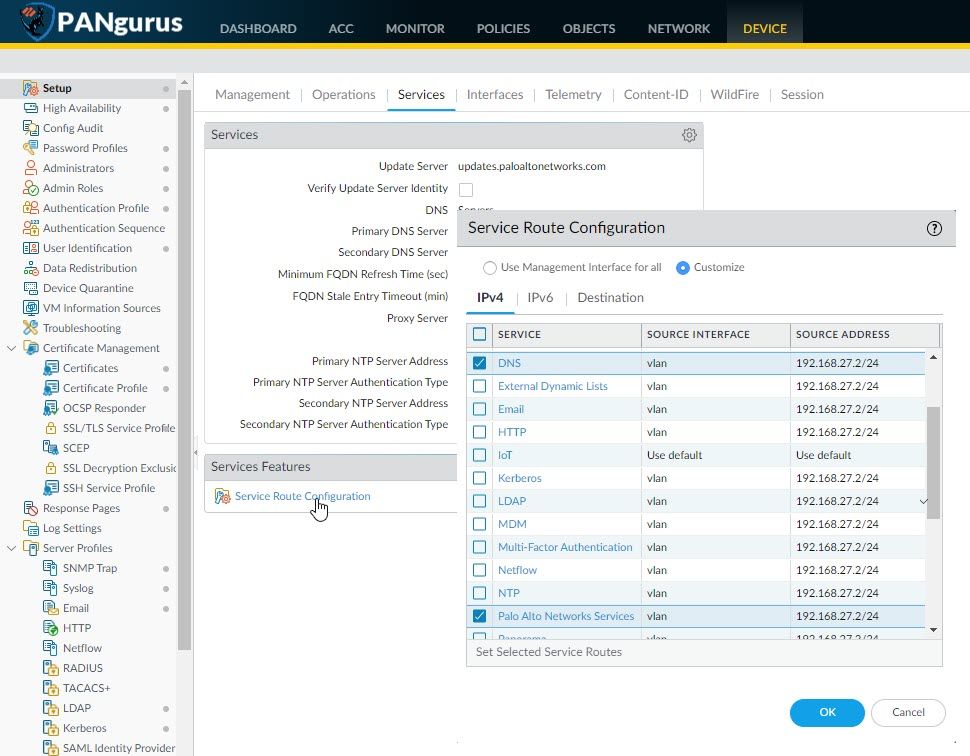
by default all connections come out of the management interface, but you can change the egress interface via service routes:
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2021 07:37 AM
Nice, I'll give it a try with this filter.
Thanks for the recommendation!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-05-2021 07:40 AM
Do you think it would be ok if I lock it down to destination FQDN Object updates.paloaltonetworks.com ?
Regards,
- 1 accepted solution
- 14851 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma AIRS AI Runtime firewall on-demand demo in AI Runtime Discussions
- Using ethernet 1/1 - 1/12 fo 10Gbps connections on a pa-3400 series firewall in Next-Generation Firewall Discussions
- Load various configuration onto staged firewall from panorama for a few attempts - remote install in Panorama Discussions
- Introducing the Strata Cloud Manager (SCM) Terraform Provider: Automate and Scale Your Network Security in Strata Cloud Manager
- Delaying upgrade between an HA pair in Next-Generation Firewall Discussions