- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Getting "engine fatal" error in Minemeld.
- LIVEcommunity
- Discussions
- General Topics
- Getting "engine fatal" error in Minemeld.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Getting "engine fatal" error in Minemeld.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2017 02:12 PM
Hi Luigi, this is in reference to ticket 00632153. Two issues here:
1. While attempting to work on issue #2, I noticed that I am getting an "engine fatal" error in Minemeld. Version is 9.34. Have restarted engine, but the issue is still there.
2. I would like to build a custom exclusion for the below Amazon IP list so that addresses are dynamically updated and can be allowed by Minemeld and an access rule in our Palo Alto that points to it. Is this possible in 9.3.4 or do I need an upgrade?
Amazon list:
https://ip-ranges.amazonaws.com/ip-ranges.json
Article you wrote about how to do this. Want to make sure that this is still the best way to do this?
thanks for all your help!
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2017 03:01 AM
Hi @BobHarrison,
there is a builtin prototype to monitor that URL aleady, it's called aws.AMAZON. There a many ways you can use this Miner, following are the 2 most common use cases:
1. Direct EDL for PAN-OS
If you want to create a feed for those AMAZON IP ranges, you can go in CONFIG > IMPORT, paste the following snippet and then press APPEND (and COMMIT :-)). You can then point PAN-OS EDL to https://<minemeld>/feeds/feedAmazonIPs.
nodes:
amazonIPs:
inputs: []
output: true
prototype: aws.AMAZON
feedAmazonIPs:
inputs:
- amazonIPs
output: false
prototype: stdlib.feedHCGreenWithValue
2. WHITELIST in MINEMELD
If instead you would like to use those IP Ranges for whitelisting indicators directly on MineMeld you can use the following snippet:
nodes:
wlAmazonIPs:
inputs: []
output: true
prototype: aws.AMAZON
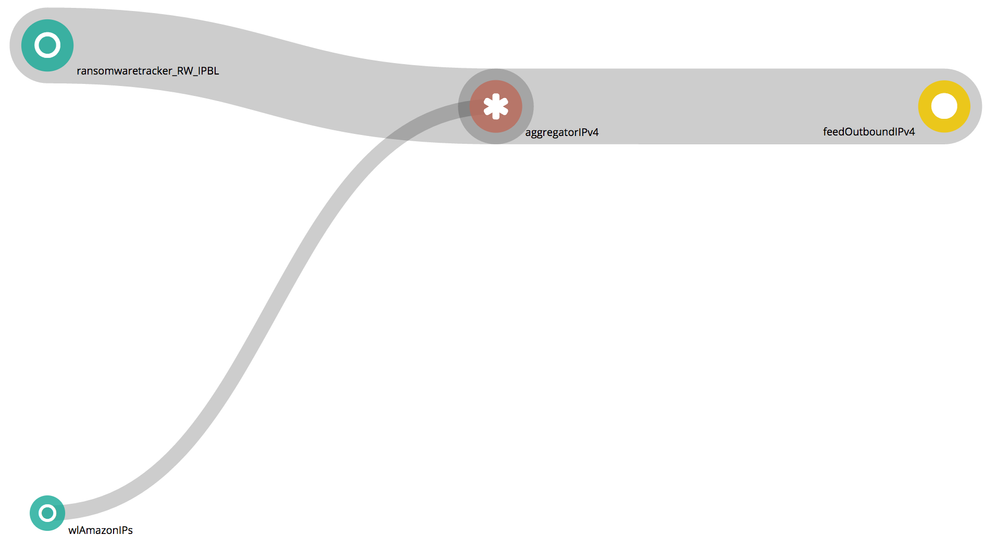
This will create a Miner for AMAZON IPs that you can connect to IPv4 aggregators to automatically remove Amazon IPs from the feeds. The trick here is the "wl" prefix in the name of the Miner. Aggregators treat as whitelist all the indicators coming from Miner starting with wl. See the example graph below, aggregatorIPv4 automatically removes indicators sent by ransomwaretacker_RW_IPBL overlapping the ranges coming from wlAmazonIPs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2017 11:18 AM
Hi Luigi, thanks for your input.
1. I am still getting "engine-fatal" issue in Minemeld?
2. What is the preferred method of the two? Currently we are using minemeld by having a DENY access-list that points to "Emerging threats feed", "high confidence feed", etc. Should I be creating a second access-list that is a PERMIT list that points to the url of our minemeld server?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2017 04:13 PM
Hi @BobHarrison,
- please, could you download and send me the minemeld-engine.log file from SYSTEM > DASHBAORD > ENGINE > LOGS ? My email address is lmori@paloaltonetworks.com
- It depends on your what is your ultimate goal. If you would like to allow all the traffic going to any AMAZON service, then the best way to do it is a new EDL pointing to the new feed. If instead you want to be sure that your OSINT feeds are not blacklisting any Amazon IP address, then you should go for solution 2) - whitelist inside MineMeld.
- 4594 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Error in MineMeld preventing communication with Palo Alto, displaying a URL error. in General Topics
- Doubt about Minemeld version 0.9.70 in General Topics
- Minemeld Webui not coming up in General Topics
- minemeld newbie in General Topics
- installing minemeld Ubuntu 20.4 in Next-Generation Firewall Discussions