- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Identify if the Palo Alto IDS/IPS has a signature for a specific vulnerability based on the CVE
- LIVEcommunity
- Discussions
- General Topics
- Identify if the Palo Alto IDS/IPS has a signature for a specific vulnerability based on the CVE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Identify if the Palo Alto IDS/IPS has a signature for a specific vulnerability based on the CVE
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-23-2020 12:44 PM
We been working with Palo Alto to identify a strategy to help identify if the Palo Alto IDS/IPS has a signature for a specific vulnerability based on the CVE number. We should roughly be able to support this use case, but there will be some limitations:
- We can verify that a signature has been downloaded to the Panorama, but NOT if it is applied to individual firewalls or individual rules.
- We can verify the DEFAULT action for a signature, but not a CUSTOM action for a signature.
Technical Details
Palo Alto downloads "content packs" which contain IDS/IPS signatures. The "content packs" are then applied to "vulnerability profiles" that are customized for "Inbound," "Outbound," etc. The "vulnerability profiles" are then applied to individual firewall rules as configured by Hershey.
Via the API, we can pull details about IDS/IPS signatures including the CVE number that it relates to. We can also pull the vulnerability profile configuration. However, we cannot link an IDS/IPS signature to a "content pack" via the API. That means that we cannot validate whether a specific IDS/IPS rule for a CVE has been applied to our environment via a vulnerability profile.
Can anyone think of a way around this?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-11-2021 08:25 AM - edited 03-11-2021 08:32 AM
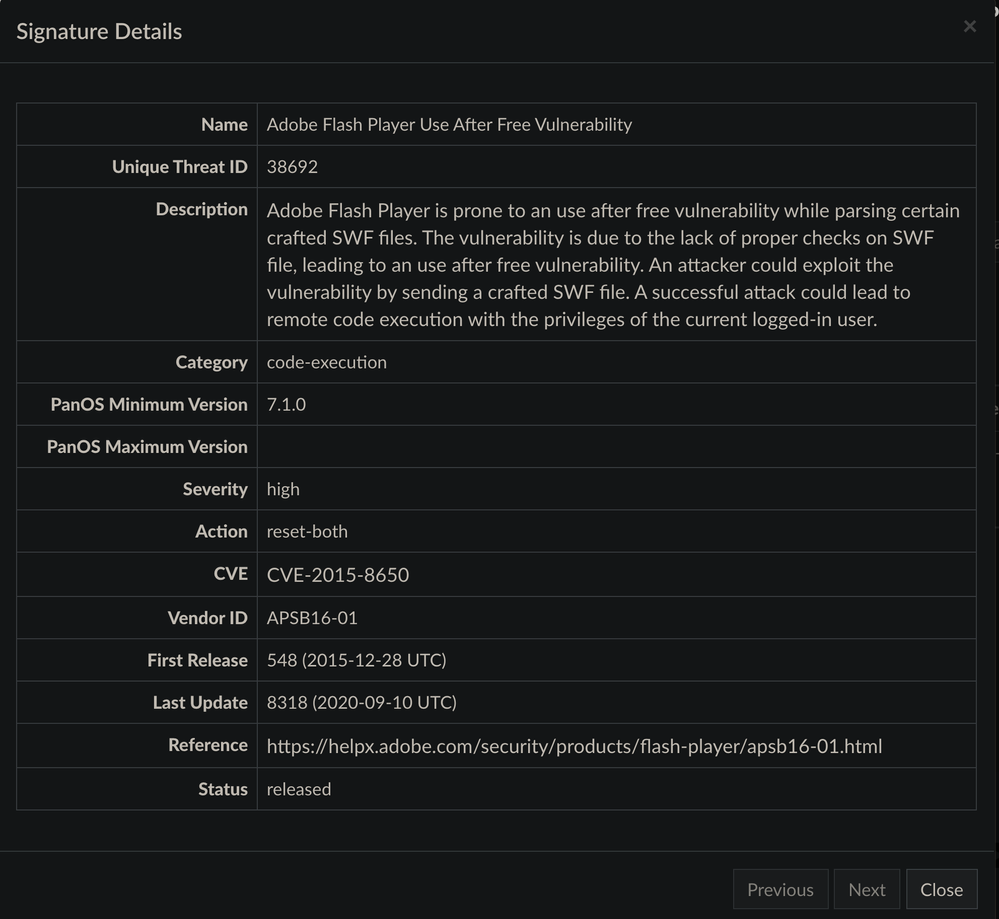
Indeed. See below example for CVE-2015-8650, wherein you are able to see the first release and recent update fields for a signature.
To access the Palo threat vault, log into your CSP account at support.paloaltonetworks.com, scroll down to resources, click threat DB, profit.
I am not currently aware of a way to access our threat vault information via API. Best practices for threat prevention includes hourly content updates with action set to download and install, for which you would be able to validate that environmental content # against a specific CVE #.
Hope this helps!
- 4826 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Cloud defender agent unable to identify Red Hat back ported patches causing false positives in Cortex Cloud Discussions
- Vulnerability Assessment in XSIAM 3.3 in Cortex XSIAM Discussions
- Threat Protection Coverage for LockBit 5.0 in General Topics
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- RealNetworks RealPlayer MPG Width Integer Underflow Vulnerability - 91059 in Next-Generation Firewall Discussions