- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Management Interface outside of firewall
- LIVEcommunity
- Discussions
- General Topics
- Management Interface outside of firewall
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Management Interface outside of firewall
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2013 11:01 AM
Knowing that one does not *usually* put a device management interface outside of the firewall, on the public Internet, in the case of PAN gateways is there any severe problem with this? I have a situation where putting the management of these devices on the private management network would require quite a bit of additional configuration, bandwidth use for updates, etc.
The only things that I have confirmed/know are listening are https/ssh/snmp, the first two of which are considered "secure". SNMP can be configured read-only easily enough.
What else would you consider a concern?
- Labels:
-
Management
-
Set Up
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2013 12:21 PM
Hi Tim,
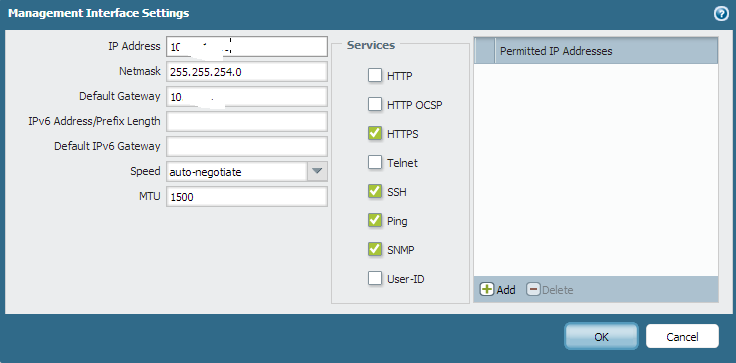
Following are the services which you can enable or disable on the management interface. You can locate this on Device tab--> setup --> management
However if you have your management traffic passing through the firewall you can create a security policy to only allow the services that you want. Make sure you still need to get software and dynamic updates from the internet.
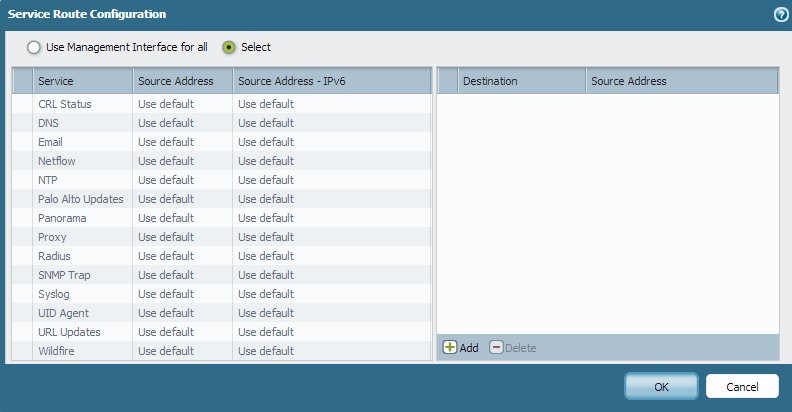
Following are the most services which takes management interface for communication unless specified differently. You can access this tab from Device tab--> setup --> services
Hope this helps.
Thanks
Numan
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2013 04:37 PM
This should be ok. Only http, ocsp, https, snmp, ping,telnet, user-id,ssh are available on management interface.
I would not allow 'ping' to allow everyone know its available.
Apart from above services, you can also restrict it to be available from only certain IPs - 'Permitted IPs'
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-28-2013 09:55 AM
Its possible to put the management interface on the outside network or on the Internet. The usual considerations apply - expose only the minimum footprint- only allow the traffic that needs to see it. In this case don't set it to respond to ICMP, only use encrypted protocols (SSL, SSH, etc.), and if at all possible limit the addresses that can login via the permitted IP list.
- 4590 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Request to locate account or transfer asset for S/N 023209008637 in Custom Signatures
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- PA-445 lost management access in General Topics
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- PA-445 setup on Mac in General Topics




