- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
SNAT to a FQDN
- LIVEcommunity
- Discussions
- General Topics
- SNAT to a FQDN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
SNAT to a FQDN
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-20-2022 11:38 AM
Hi All,
I am trying to create a NAT policy that would NAT traffic from my internal Zone to and update server.
the problem is i have FQDN of destination server which resolves to multiple different IPs.
I need to find a way to complete this NAT policy, is there any way i can make this work?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-25-2022 03:14 AM
Hi @mike.07 ,
In the NAT rule, you can specify an FQDN as an object just as long as the Palo can resolve the FQDN.
Stay Secure,
Jay
Don't forget to Like items if a post is helpful to you!
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-04-2022 12:06 AM
Hello, im a new PaloAlto User and run in some problems too.
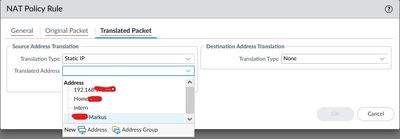
For testlab i need fqdn Source NAT.
But i cant use the Adress added at "Adresses" and add it as a source at NAT...
PA can resolve the FQDN.
Anything im missing?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-04-2022 01:07 AM
Hello @maniac72
I think you have a little wrong concepto to apply NAT in Palo Alto.
I suggest review this links:
https://docs.paloaltonetworks.com/pan-os/9-1/pan-os-admin/networking/nat/nat-configuration-examples
https://www.packetswitch.co.uk/palo-alto-nat-example/
Best regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-04-2022 01:50 PM
Hello:
I understand more or less what you want or wish to do as a goal:
When you create as Address type FQDN, you place the subdomain and Palo Alto will be in charge of resolving at DNS level. That if the Palo Alto must be able to connect with one or two DNS servers, to be able to resolve these addresses. If the Palo Alto does not have DNS set up it will not be able to resolve these addresses.
I understand that what you want is that when traffic goes to a certain destination, example a FQDN, example:
www.testingfqdn.com ----> 1.2.3.4/32
Well if that is what you want to do, when it goes to that destination apply a Source NAT, what you should do is the following:
First, you must set the corresponding zones, source, e.g. your network/LAN zone, destination your outside/Untrust Internet zone. Now in the original packet section, in destination, instead of any, put your FQDN. Now in the translation section, in the "Source translation" section, enter the IP with which you are going to translate the traffic, e.g. the outgoing interface, if it were a public IP, then select the Untrust interface and the Public IP of your interface.
Now if you are looking to do a DNAT or PortForwarding the configuration is somewhat different.
Here are a couple of sites/links to guide and support you:
https://docs.paloaltonetworks.com/pan-os/9-1/pan-os-admin/networking/nat/nat-configuration-examples
https://www.packetswitch.co.uk/palo-alto-nat-example/
Best regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-06-2022 11:17 PM
Good morning,
thanks for your feedbacks.
Maybe i´ve to explain it a little more
In my testlab i have a dynamic IP from my provider.
In front of the Palo ther is another Router, connecting to the Internet
Normaly i would change the router to Modem only, but there a my also my Telef´phones connected, so i cant switch it
I read some different posts about Source NAT to get the external IP with a DynDNS service
https://www.wirelessphreak.com/2019/01/pan-firewall-and-xbox-nat.html
https://live.paloaltonetworks.com/t5/general-topics/dynamic-ip-isp-nat/td-p/103703
What i understand:
I need to SNAT the traffic from the internal host to my external IP
I need to NAT the traffic coming from external to my internal host
In the LAB this are two services
The Xboxes
And a acme bot for lets encrypt certificates
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-06-2022 11:31 PM
Hello @maniac72
OK ok, that's another thing.
Yes I have implemented scenarios with DYNDNS, for example Palo Alto's Global Protect VPN service.
So if for some reason, you need to expose your xbox among other equipment to be accessed from the Internet, but you don't have a Static Public IP.
I recommend:
On the modem, configure the DYNDNS service so that the Modem, which has dynamic Public IP addressing, publishes and updates the IP.
Now with that done, in the same ISP modem, you can configure a DMZ or Port Mapping specific to a certain IP/Ports will be, the External interface of your Palo Alto, which I imagine has an IP in the same LAN range, of your Modem.
Well then it looks like this:
IPdynamic-Internet----Modem ( Config DYNDNS user password host )-----Interconnection Palo Alto----Interface External Firewall Palo Alto--- DNATs on Palo Alto to your local resources and devices.
With that scheme, point everything to the Modem, to the Dynamica public Ip, then either use DMZ to forward all external traffic to the Palo Alto external IP or The Ip and certain Ports, then just do the DNATs you require on the Palo Alto and also a Source Nat, so that your devices can go out to the Internet through the Palo Alto and then they go out with an IP of the range of your LAN of the Modem and already, it is not complex at all, just make sure to configure DYNDNS in the modem, then point to the external IP of the Palo Alto and then in the Palo Alto configure the Destination Nats that you require, and that's it.
Best regards
- 5769 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Purpose of .prod.reporting.paloaltonetworks.com in Strata Cloud Manager in Strata Cloud Manager
- Username Generalization Playbook in Cortex XSIAM Discussions
- VPN peer ID in Next-Generation Firewall Discussions
- Handling voip behind ION 1200S in Prisma SD-WAN Discussions
- NAT Policy Zone Selection for DNAT (and DNAT+SNAT) — Is My Understanding Correct? in Next-Generation Firewall Discussions