- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
User-id with internal portal
- LIVEcommunity
- Discussions
- General Topics
- User-id with internal portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
User-id with internal portal
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2020 03:50 PM
Hello community,
I have just started my journey to PA world and spend several days configuring global protect features.
I successfully configured portal for as internal point of connection for Global protect client.
Idea is to provide User-id information to firewall without VPN connection.
As result my GP client tells me that "you are connected to internal network" but under PA device I don't see user<->ip information. User-id based rules don't work. no information from "show user ip-user-mapping all."
1. Are there any additional steps required to enable User-id features. I enable it only at security zone level.
2. Would it be possible to have one portal but two gateways (ext, int) for internal (user-id provisioning only ) and external (vpnssl) deployments. Or there are two portals external / internal are required ?
Thanks in advice !
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2020 04:30 PM
Do you mean interface where portal is hosted !
Thanks for reply !
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2020 05:14 PM
That's correct. Say for example I'm using the interface ethernet1/2 for the internal gateway and you have that assigned to the default 'trust' zone, you'll need to ensure that you have user ID enabled for the zone.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2020 03:58 AM
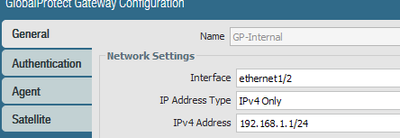
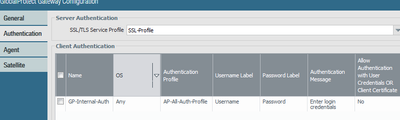
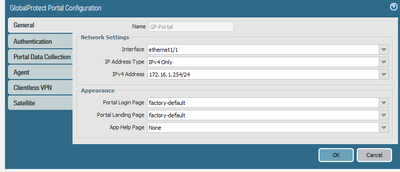
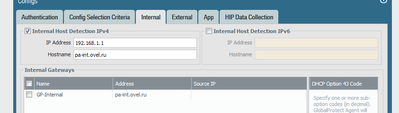
So I believe you're looking for how to authenticate logged in users whether they're outside or inside. I've spent 2 ways on how to do it, the documentation is not describing it clearly. You need to have 2 gateways for this, one external, and one internal one. The internal gateway can be your firewall interface inside IP address, the main trick is here:
this IP must be resolvable into your internal hostname you specified in the portal config in both ways: in the direct internal DNS resolution, and also reversed DNS resolution.
In my example I have the inside L3 interface with the IP 192.168.1.1. In my internal DNS there is an A record pa-int.ovel.ru pointing to this IP, and ALSO there is reversed zone arpa.1.168.192 that resolves .1 into pa-int.ovel.ru.
The gateway config is here:
Authentrication
And then the portal config is here:
Internal Gateway:
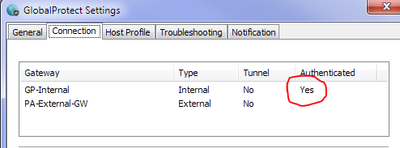
And after that your GlobalProtect should be able to get your user authenticated straight away.
And yes, it's very important: All this is working in "Always-On" mode only!!! At least in my case.
Hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2020 06:22 AM
Ovel , hi !
Appreciate your detailed instruction.
I started from very simple scenario , just internal portal without Gateway detection.
As I said GP shows that "you are in internal corporate network" but under Connection tab I don't see "YES" as you marked in red.
I have "user-id" enable on all zones as soon as my device is in lab mode at this moment.
only two reasons which I see right now :
1.certificate issues/ because I have self-signed , and some errors under GP client logs.
2. user-id matching problem. Because under monitor->global protect-> source user shows as domain\username. Might it be the problem ?
Under monitor->user-id - i don't see anything .
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2020 07:05 PM
Hi Eronko,
The certificate is not so important at this stage, i also have a self signed one, but it's better if your GP client would install the firewall Root CA into the host PCs if you plan to use SSL Decryption. You don't need to enable user-id on the outside zone. The outside zone is not supposed to identify users, it's the gateway's role on that side. What is important though is that your internal users have to be able to reach your external gateway IP from inside. In my understanding when GP client is trying to authenticate the user, it goes to the external gateway, authenticate it over there as per your auth profile, and only AFTER that it checks whether the user is internal or not.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-24-2020 01:25 AM
Hi,
My issue was resolved after some GP client analizis from my side.
Misconception was that I used IP (FQDN ) in configuration of connection between Portal and Gateway. As result GP authenticates well on portal but returns logs warrings for gateway because i have WC certificates . As soon as I moved config to FQDB based approve it works well.
Appreciate everyone assistance !
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2024 02:29 PM - edited 09-12-2024 02:30 PM
Hi any chance you can share the config for this setup you did please ?
- 12830 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect Connectivity Issue in GlobalProtect Discussions
- One portal, multiple gateways for different users in GlobalProtect Discussions
- Auto connect based on interesting traffic in GlobalProtect Discussions
- GlobalProtect Gateway on PA-820 Stopped Responding – Guidance Needed in GlobalProtect Discussions
- Clientless VPN and Remote Desktop in Next-Generation Firewall Discussions