- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
August 2022 Rewind: Here's What You Missed on LIVEcommunity
- LIVEcommunity
- Get Started
- News
- August 2022 Rewind: Here's What You Missed on LIVEcommunity
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 08-31-2022 07:58 AM - edited on 09-06-2022 08:36 AM by jennaqualls
Welcome to our August 2022 Rewind, where we reflect on LIVEcommunity’s biggest headlines.
This past month, we shared information about the upcoming SASE Converge virtual conference; new features in Prisma Access 3.2; a community feature we're calling Nominated Discussions; a new Prisma SD-WAN customer journey guide; and more! Read on to learn about LIVEcommunity’s August 2022 highlights.
Join Industry Experts At SASE Converge 2022 (Sep 13-14)
Is your network ready for a new hybrid work environment? Join Palo Alto Networks leadership and industry experts at SASE Converge 2022, the industry’s premier SASE event, to learn about the latest trends and innovations.
Here are some session highlights from the upcoming virtual conference, happening September 13-14:
- Ushering in the New Era of Work with ZTNA 2.0 (KEYNOTE)
- Why Your SASE Deployment Should Start with ZTNA 2.0
- A Pragmatic Approach to Implementing Zero Trust with SASE
- Modernizing Networking and Security for Hybrid Work Era: Insights from Customers
Register for SASE Converge 2022 now.
New Features Introduced in Prisma Access 3.2
Prisma Access helps you deliver consistent security to your remote networks and mobile users, giving protection at scale with global coverage—so you don’t have to worry about things like sizing and deploying firewalls at your branches, or building out and managing appliances in colocation facilities.
Learn about the new features and behavior introduced with the release of Prisma Access 3.2.
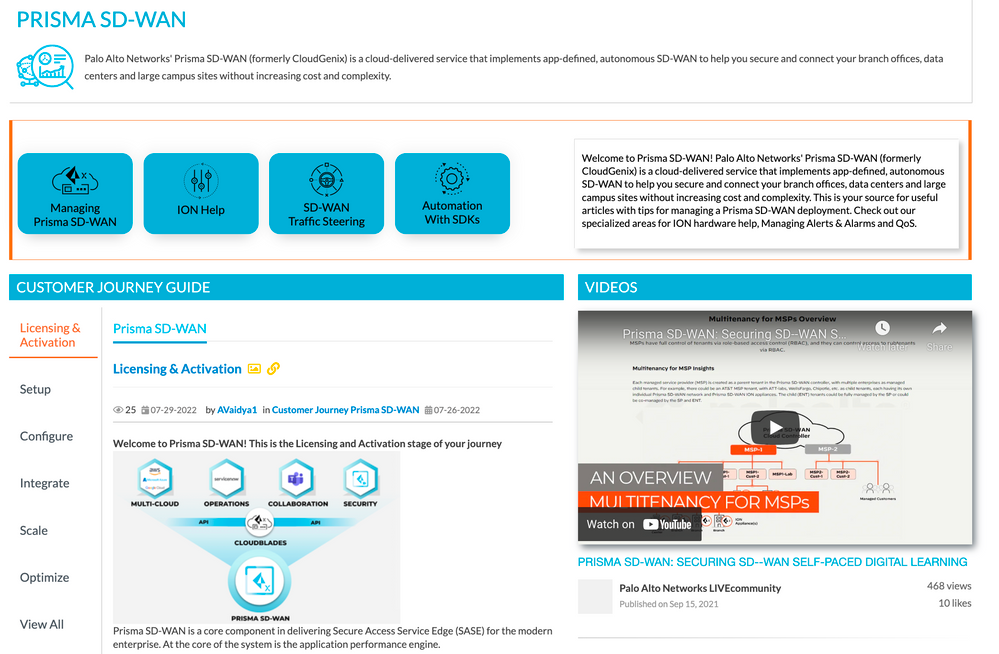
Prisma SD-WAN Customer Journey Guide + Self-Help Resources
We are excited to share LIVEcommunity's new Prisma SD-WAN Customer Journey Guide! This guide, plus new innovative self-help resources added to the Prisma SD-WAN product page, will help customers adopt and deploy their products with ease.
Introducing Nominated Discussions-to-Articles for the Community Knowledge Base
LIVEcommunity moderators can now nominate a discussion topic to be an article. This is a great way for members to be able to contribute to our community knowledge base. Here’s a list of member-posted discussions we’ve turned into articles so far:
- Nominated Discussion: Security Policy - US access only
- Nominated Discussion: Web-Gui Access With No Secure Certificate
- Nominated Discussion: Web-Gui Access With No Secure Certificate
- Nominated Discussion: Best practices - Multi large upgrades pan-os Firewall HA
- Nominated Discussion: Disable Local Account When NAC is Reachable
Thank you for contributing meaningful topics, replies, and solutions to LIVEcommunity's reservoir of knowledge!
Updates to LIVEcommunity's CN-Series Product Page
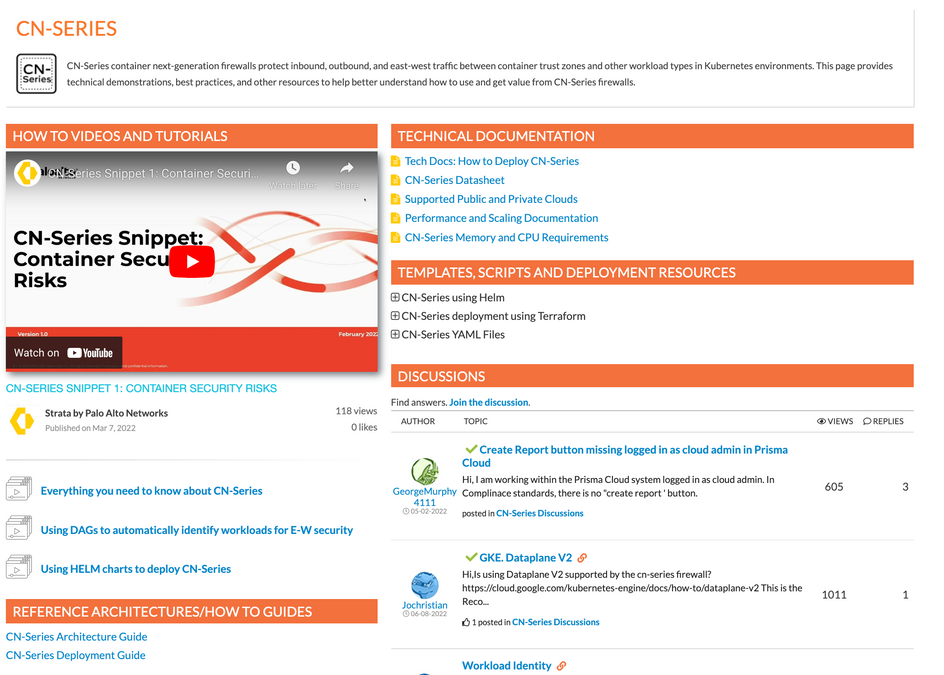
The CN-Series product page now includes new areas such as technical documentation, templates, scripts, deployment resources, and how-to guides. Check out the changes now, and let us know what you think.
August 2022 LIVEcommunity Member Spotlight: @Kadak
For the August 2022 Member Spotlight, we’d like to applaud one of our community members, @kadak, for their participation and engagement in the LIVEcommunity! Since joining the community in November 2011, they have written 259 posts, received 125 likes, and authored 82 solutions (and counting).
Thank you for your contribution and participation in the community @kadak!
Introducing: Unit 42 MDR and Cortex XDR 3.4
More and more enterprises are reaching out to Managed Detection and Response providers (MDR) to increase their security posture. This is an increasing trend because the threat landscape is becoming more and more complex and the attack surface keeps getting bigger. Many companies reach out to MDR to offload investigating, responding to and managing alerts. That's why Palo Alto Networks recently launched the Unit 42 MDR service, an MDR service for Cortex XDR, delivered by the Palo Unit 42 team. Our experts will work for you 24/7 to stop attacks with continuous monitoring, proactive threat hunting, alert triage, investigation and response services allowing your team to focus on what matters. Learn more here.
Defense-in-Depth Strategy With WAF and VM-Series NGFW
Cyber attacks have become more sophisticated today. This new reality is motivating organizations to opt for defense-in-depth strategies across their on-prem, private, and public cloud deployments. The defense-in-depth approach implements multiple layers of security to reduce the attack surface. Together, Web Application Firewall (WAF) and VM-Series firewall provide comprehensive security, particularly for customers who want to provide a Zero Trust security method to protect not just inbound, but also outbound and east-west traffic. Read this expert-written blog to learn more about the capabilities of these two solutions.
Cloud NGFW Video: Outbound Decryption Setup
The latest in our Cloud NGFW how-to video series, this tutorial shows customers how to configure Outbound decryption in a few simple steps.
Tips & Tricks: What You Should Know About Threat Reporting
As the attack surface keeps getting bigger and attacks are becoming more and more sophisticated, threats are a huge concern for any security professional. The amount of information you get might be overwhelming and it might be difficult to know where to start.
So let's start with the Threat Logs. You will find these inside the WebGUI > Monitor > Threat tab. There, you'll see events ranging from informational to critical in severity. See the example below, where I'll use a Critical event as an example.
Adding Locally Managed Firewalls to Panorama Management
When migrating locally managed firewalls, plan the transition to Panorama Management. Determine which firewalls are going to be managed by Panorama and start to plan the device group hierarchy, templates, and template stacks for the environment. It is important to keep in mind which firewalls will share common policies when designing the structure.
You're now fully briefed on LIVEcommunity's August 2022 highlights!
If this was helpful, be sure to give this blog a thumbs up. See you next month!
- 6100 Views
- 0 comments
- 1 Likes
-
2.3 Network Integration
1 -
Alibaba Cloud
1 -
April
1 -
Azure
1 -
Best Practice Assessment
1 -
BPA
1 -
Certification
4 -
Community
5 -
community news
31 -
Community Updates
4 -
Cortex
1 -
Cortex Data Lake
1 -
Cortex XDR
1 -
Cortex XSOAR
1 -
Cyber Elite Program
1 -
cyberelite
8 -
events
2 -
Expedition
1 -
GlobalProtect
1 -
Google Chrome
1 -
Ignite '22
1 -
Ignite 2022
1 -
LIVEcommunity
12 -
member testimonials
1 -
Network Security
1 -
News
8 -
NGFW
6 -
PAN-OS
3 -
Panorama
1 -
Prisma Access
2 -
Prisma Cloud
1 -
Rewind
20 -
Skillets
1 -
Strata Logging Service
1 -
Tips & tricksm
1 -
Tips and Tricks
1 -
VM-Series on Azure
2 -
webinar
1 -
XSIAM
1
- Previous
- Next