- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
CN-Series Part 3: CN-Series Use Cases
- LIVEcommunity
- Products
- Network Security
- Next-Generation Firewalls
- CN-Series
- CN-Series Articles
- CN-Series Part 3: CN-Series Use Cases
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 08-05-2021 08:49 AM - edited on 08-05-2021 10:26 AM by jforsythe
In our previous blog Why Did We Build the CN-Series?, we discussed what is CN-series and how to deploy it natively using Helm Charts. Today, we're going to walk through prominent use cases.
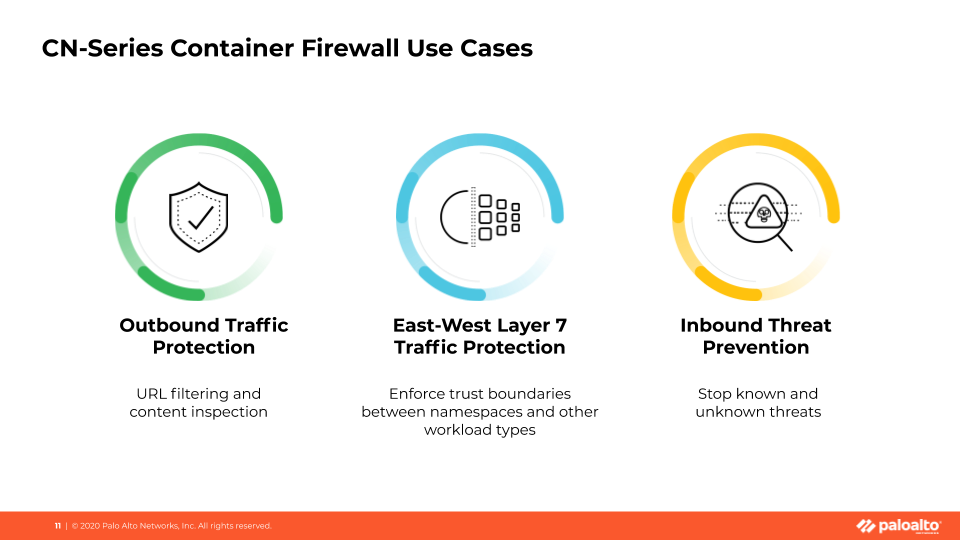
There are three use cases in which customers most often employ CN-Series container firewalls. All three of these examples involve the insertion of threat protection—and other advanced security services—at the trust boundaries of cloud-native applications.
Use Case #1: East-West Layer 7 Traffic Protection
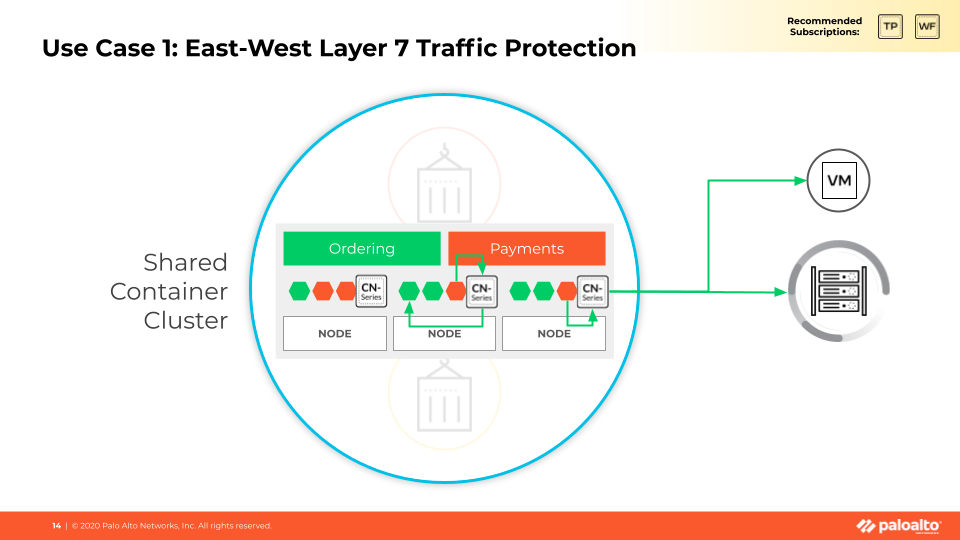
First up is the east-west traffic use case. Customers can use CN-Series to insert Layer 7 traffic protection and advanced threat-protection into their Kubernetes environments—this secures the allowed connections between two containerized applications of different trust levels; it can also secure the allowed connections between containers and other workload types.
Other micro-segmentation products provide granular protection at Layers 3 and 4 to block traffic between workloads that shouldn’t be able to communicate. The critical difference is that CN-Series can inspect and control allowed traffic at Layer 7 and enable our Threat Prevention subscription service to detect and stop threats that may be attempting to move laterally across the environment. The two types of solutions absolutely can be used together.
Read Part 1: What is CN-Series? now.
Use Case #2: #Outbound Traffic Protection
The second prominent use case is securing outbound traffic from container environments to the internet or developer resources hosted in sites like Github. Our URL-filtering service provides guardrails for developers and other users to ensure they aren’t connecting to potentially malicious sites. Our firewall’s ability to inspect traffic content, coupled with our DNS Security service guard against data exfiltration, ensures our customers’ critical information stays in the environment where it belongs.
While some customers may prefer to use their perimeter firewalls in their on-prem data centers, customers running Kubernetes environments in the public cloud will require CN-Series to solve this use case. Here is a quick video demonstration, Outbound Traffic Protection Using CN-Series Container Firewall, for your reference.
Read Part 2: Why Did We Build the CN-Series? now.
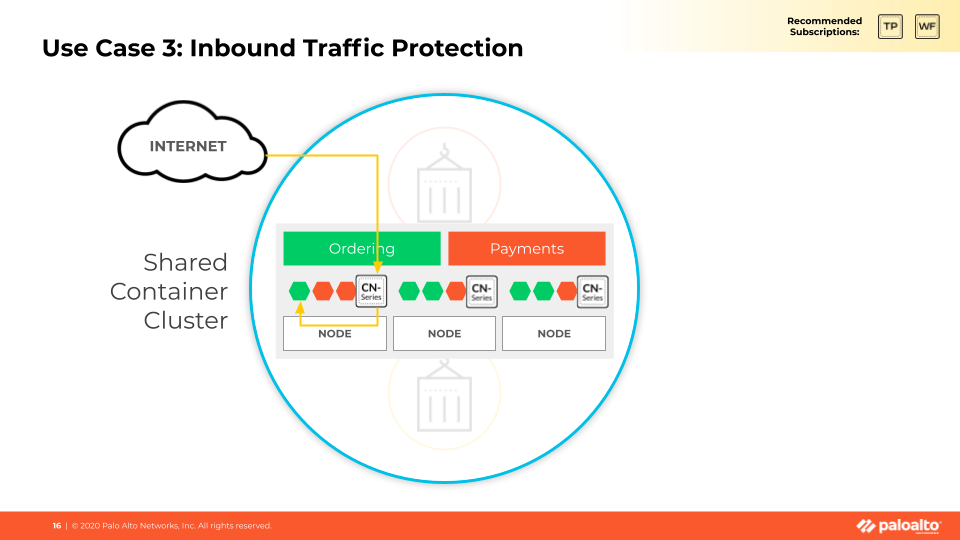
Use Case #3: Inbound Threat Prevention
Last but not least is the traditional inbound perimeter use case. Network security teams can prevent threats riding on inbound traffic to the container environment with our Threat Prevention and Wildfire malware analysis services. Again, depending on the customer’s environment and overall architecture they may elect to do this with their perimeter firewalls on-prem. Still, a CN-Series or VM-Series would be required to do this in public cloud environments.
All three of these use cases can be addressed regardless of whether the apps are hosted in an on-prem data center or a public cloud.
To summarize, CN-Series container firewalls deliver:
- Inline network security to improve visibility and protect Kubernetes namespace boundaries with security services such as threat protection and URL filtering.
- Flexible configuration and deployment options to allow administrators to automate security deployment and leverage the autoscaling capabilities of Kubernetes.
- Cloud and on-premises support to give network architects the tools to design public, private, and hybrid cloud architectures.
- Centralized security management via Panorama to unify control of hardware and virtual Palo Alto Network firewalls as well as native security provided by Amazon Web Services, Google Cloud, Microsoft Azure Kubernetes Services and OpenShift.
Find more information about Secure Your Kubernetes Future with CN-Series Container Firewalls.
Find the entirety of the three-part CN-Series by Raj Patil on our CN-Series Articles page.