- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Policy-Based Forwarding Symmetric Return Overview
- LIVEcommunity
- Articles
- General Articles
- Policy-Based Forwarding Symmetric Return Overview
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
This article was created by @aalex
Enabling symmetric return ensures that return traffic is forwarded out through the same interface through which traffic ingresses. This feature is useful when the requirement is to access servers through two ISP connections (on different ingress interfaces) and the return traffic must be routed through the ISP that originally routed the sessions.
This feature is also required for asymmetric routing environments.
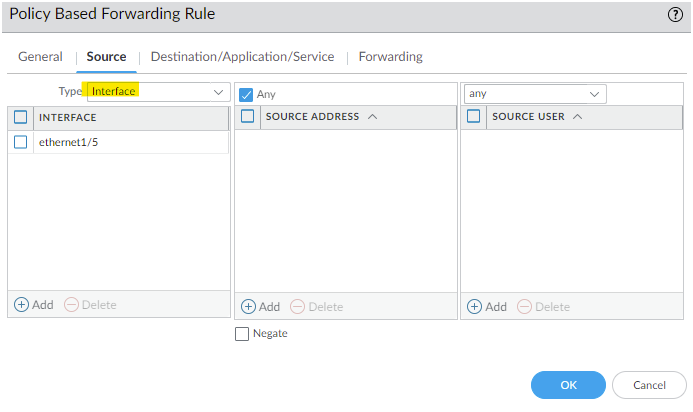
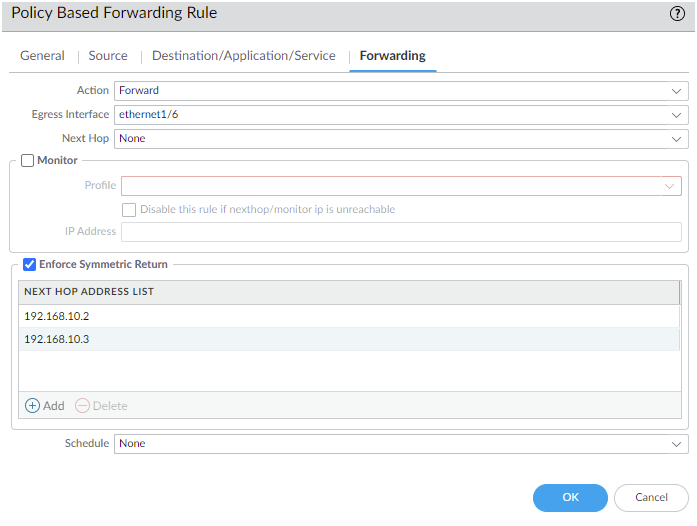
The feature is configured under Policies > Policy Base Forwarding > Open an existing rule, or click Add to create a new one > Forwarding. Tick the Enforce Symmetric Return button to enable the feature.
Note: If the client-to-server traffic does not need to be forwarded to a specific egress interface or next hop then the Forwarding > Action can be set to No PBF. This prevents the alteration of the path that the client-to-server packets take, which lets the matching client-to-server packets use the normal route table path while the server-to-client packets still benefit from the symmetric return feature.
Things to keep in mind regarding next hop addresses:
- Configuring next hop addresses in the Next Hop Address List is optional, but forwarding may fail when Enforce Symmetric Return is enabled without a next hop address. Click here for more details.
- Up to 8 next hop addresses can be defined per PBF rule.
- PBF rules will not use the symmetric return option if the packet's source IP address is in the same subnet as the symmetric return address.
The following command can be used to monitor the return-mac entry table:
admin@VM-1> show pbf return-mac all
current pbf configuation version: 1
total return nexthop addresses : 0
index pbf id ver hw address ip address
return mac egress port
--------------------------------------------------------------------------------
maximum of ipv4 return mac entries supported : 1250
total ipv4 return mac entries in table : 0
total ipv4 return mac entries shown : 0
status: s - static, c - complete, e - expiring, i - incomplete
pbf rule id ip address hw address port status ttl
--------------------------------------------------------------------------------
maximum of ipv6 return mac entries supported : 500
total ipv6 return mac entries in table : 0
total ipv6 return mac entries shown : 0
status: s - static, c - complete, e - expiring, i - incomplete
pbf rule id ip address hw address status
--------------------------------------------------------------------------------
This return-mac table can be cleared manually with the following commands:
> clear pbf return-mac name <value>
or
> clear pbf return-mac all
Notes regarding the return-mac table:
- The return-mac table size is always half of the ARP table entry size based on the firewall model. This capacity applies per device and is not limited per vsys.
- The displayed entries in the table, as well as the total entries counter, only show the information from the current vsys.
- To change the vsys information being displayed, change to a different vsys and re-run the command:
> set system setting target-vsys <vsys-name>
once done, set it back
> set system setting target-vsys none
- The unused entries remain in the table for 30 minutes before getting timed out and flushed automatically.
- If a symmetric return next hop address is not configured, then the packet's source MAC address is used as the return-mac.
- If a symmetric return next hop address is configured, then the packet's source MAC address is also used as the return-mac, but if the return-mac table reaches 80% of its capacity then new return-mac entries are no longer populated in that table and the return-mac falls back to using the configured next hop's MAC address.
- If there are multiple IP addresses configured in the Next Hop Address List then the first one that is accessible (ARP resolved) will be selected as the next hop.
- There are no logs/alerts triggered once the return-mac entries threshold is reached.
The following should also be noted when using the symmetric return feature:
- The Source > Type of the PBF rule must be an interface, not a zone.
- The symmetric return option can be used for all Layer-3 interfaces, except loopback interfaces. It is also supported for interfaces that have the IP address assigned dynamically (DHCP and PPoE).
- The next hop address list is not supported for tunnel and PPoE interfaces.
- If an interface has multiple PBF rules, only one rule can enforce symmetric return.
- If the same source IP address is expected to come in from different ingress interfaces, then the return traffic for this client may flap in between the ingress interfaces when hardware offloading is involved. It is suggested to configure separate symmetric-return PBF rules for each ingress interface to avoid this.
Additional Information
Additional details about Symmetric Return configuration with examples can be found here.
What happens if you use Source Zone instead of Source Interface while enabling Symmetric Return?
PPPoE 回線に PBR の 'symmetric return' を指定する場合、next-hop アドレスを指定できません。
対向機器は ISP のルーター 1台でも return-mac table の溢れに注意する必要がありますか?
- 28095 Views
- 2 comments
- 1 Likes
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
8 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CICD integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud logging
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Compliance
1 -
Configuration
9 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSIAM
1 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
Dual Forwarding
1 -
dual forwarding behavior
1 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
fire and forget logging
1 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector
1 -
Log Collector Design
2 -
Log Collector vs SLS
1 -
Log Management
1 -
Logging
1 -
Logging & Reporting
1 -
login
1 -
Logs
3 -
logs missing in SLS
1 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Dual Forwarding Mode
1 -
PAN-OS log forwarding
1 -
PAN-OS log loss
1 -
PAN-OS logging
1 -
PAN-OS logging architecture
1 -
PAN-OS migration to SLS
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Single Forwarding
1 -
Site-to-Site VPN
1 -
SLS best effort delivery
1 -
SLS log delivery
1 -
SLS log fidelity
1 -
SLS missing logs
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
3 -
Strata Logging Service (SLS)
1 -
Strata Logging Service troubleshooting
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Technical Architecture
1 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next