- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Tips & Tricks: Commit & Config Locks
- LIVEcommunity
- Articles
- General Articles
- Tips & Tricks: Commit & Config Locks
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 05-09-2023 11:14 PM
Palo Alto Networks' Commit and Config Locks are important features that help ensure the integrity of network configurations and prevent unauthorized changes.
The Commit operation, in Palo Alto Networks devices, is the process of applying configuration changes made to the device to the running configuration. It is an essential step in the configuration process, as it allows the changes to take effect and be enforced. Before committing configuration changes, administrators can preview the changes and validate them to ensure that they are accurate and won't cause any disruption to the network.
Once the Commit operation is executed, the changes are written to the device's configuration and are applied to the running configuration. The configuration changes are then saved to the device's non-volatile memory, making them permanent.
In a team where multiple admins are responsible for the same systems, one always needs to coordinate config changes to prevent someone from pushing out or committing a change while someone else is still making changes, potentially committing an invalid or horribly wrong configuration.
To help prevent these kinds of conflicts, two kinds of locks are available to administrators: Commit Locks and Config Locks
As the name implies, a Commit Lock will prevent other admins from committing anything to the firewall until the lock has been released. This lock can be configured to be automatically acquired as soon as one administrator makes a change:

If one administrator makes a change and a second admin logs on and changes something, then tries to commit, they will be presented with a message saying that other administrators are holding a commit lock.
The lock needs to be cleared by the first administrator committing his configuration or relinquishing his lock to the second admin.
A lock can also be set manually, by clicking the little lock icon in the upper right-hand corner and selecting the type of lock:
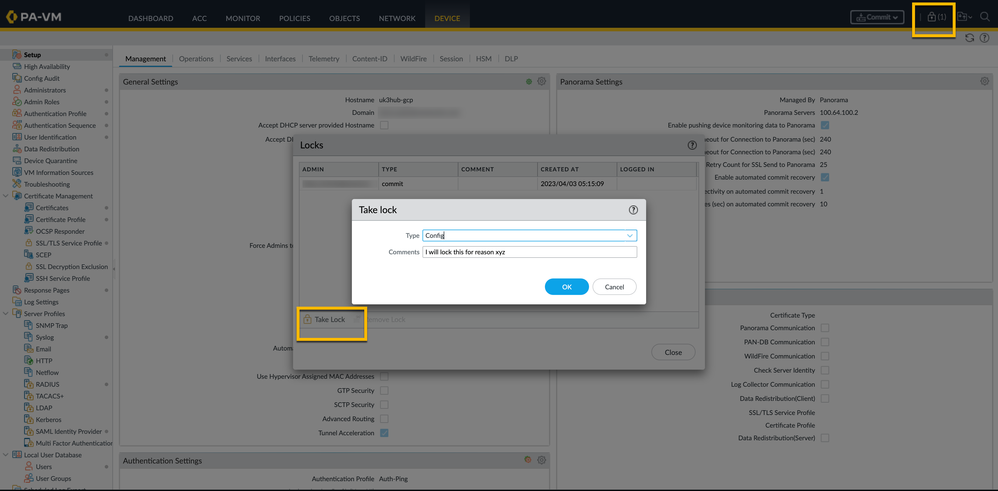
Config Locks are a feature in Palo Alto Networks devices that prevent multiple administrators from making changes to the device's configuration at the same time. This feature is important in environments where multiple administrators may be working on the same device simultaneously, as it prevents conflicting changes that could cause disruptions or security vulnerabilities.
When a Config Lock is applied, only the administrator who holds the lock can make configuration changes to the device. This prevents other administrators from making changes that could conflict with the changes being made by the locked administrator.
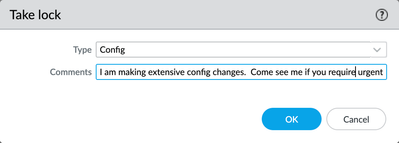
You can also add a short description of what you are doing to notify other administrators of your activities.
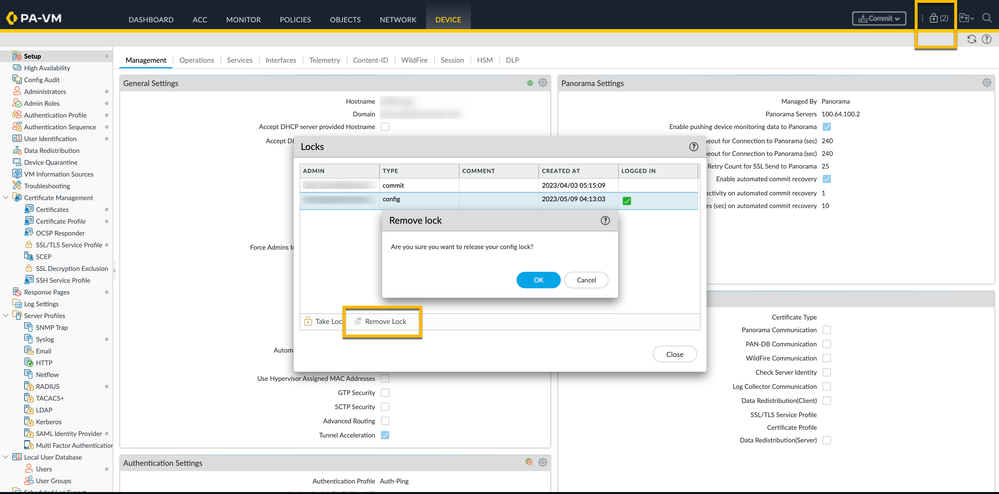
Config Locks are also helpful in preventing unauthorized changes to the device's configuration. If an unauthorized user attempts to make changes to a device that is currently locked, the device will reject the changes, and an alert can be generated to notify administrators of the attempted change. Anyone trying to change the configuration will be greeted with an error message saying the "Configuration is locked".
If required, a lock can be removed by the administrator who acquired the lock, or a superuser.
By combining the Commit and Config Lock features, Palo Alto Networks devices can ensure that configuration changes are made securely and with minimal disruption to the network. Before committing any changes, administrators can preview the changes and validate them to ensure they are correct.
This combination of features helps ensure the integrity of network configurations and prevents unauthorized changes.
- 14145 Views
- 0 comments
- 2 Likes
- Tips & Tricks: Palo Alto Global Counters for Layer 1 to Layer 4 issues troubleshooting like MTU and DOS in General Articles
- Demystifying Selective Push on Panorama in General Articles
- Best Practices for Configuration Management Performance on Panorama in General Articles
- Nominated Discussion: Palo Alto Networks Firewall Commit Error in General Articles
- Nominated Discussion: FIPS-CC Mode Initial Setup in General Articles
-
"Address Objects"
1 -
10.0
1 -
10.1
1 -
10.2
2 -
ACC
1 -
Active-Passive
1 -
AD
1 -
address objects
1 -
admin roles
1 -
Administration
6 -
Administrator Profile
1 -
ADNS
1 -
Advanced DNS Security
1 -
Advanced URL Filtering
2 -
Advanced WildFire
1 -
AI
2 -
AI Security
1 -
AI Threat
1 -
AIOPS
1 -
Analytics
1 -
Ansible
2 -
antivirus
1 -
API
2 -
API & SDK
1 -
App-ID
1 -
applications
2 -
APS
1 -
Artificial Intelligence
1 -
Asset Management
1 -
Authentication
6 -
Authentication Profile
1 -
Authentication Sequence
1 -
automatically acquire commit lock
1 -
Automation
6 -
AWS
3 -
Basic Configuration
4 -
Beacon
1 -
Best Practices
7 -
Block List
1 -
Cardinality
1 -
categories
1 -
certificates
1 -
Certification
1 -
Certifications
1 -
Certifications & Exams
1 -
CI CD Integration
1 -
CLI
5 -
CLI command
3 -
Cloud Automation
1 -
Cloud Identity Engine
1 -
cloud ngfw
1 -
Cloud security
2 -
Collector Group
1 -
Commit and Push
1 -
Commit Process
1 -
Configuration
8 -
Configuration and Management
3 -
Configure Next Generation Firewall
1 -
console
1 -
Container
1 -
Cortex
1 -
Cortex Data Lake
2 -
Cortex XDR
3 -
Cortex XSOAR
2 -
CPSP
1 -
Custom Signatures
3 -
custom-featured-post
1 -
cyber elite
1 -
cyberelite
13 -
Cybersecurity
1 -
dag
1 -
DDoS
1 -
Debug
1 -
debugging
2 -
Default Policy
1 -
discussions
1 -
DLP
1 -
Docker
2 -
EDL
2 -
education
1 -
Education and Training
1 -
Education Services
1 -
Educational Services
1 -
Effective Routing
1 -
End to End Encryption
1 -
Endpoint
1 -
export
1 -
failover
1 -
FAQ
1 -
file upload
1 -
Filtering
2 -
Firewall
2 -
Firewall VM-Series
2 -
Focused Services
3 -
Focused Services Proactive Insights
2 -
gateway
1 -
Gateway Load Balancer
2 -
GCP
3 -
GCP Firewall
1 -
geolocation
1 -
Getting Started
1 -
GitHub
1 -
GKE
1 -
Global Protect
1 -
Global Protect Cookies
1 -
GlobalProtect
7 -
GlobalProtect App
1 -
globalprotect gateway
1 -
GlobalProtect Portal
2 -
google
2 -
Google Cloud
4 -
google cloud platform
2 -
Hardware
2 -
Header Insertion
1 -
High Availability
1 -
How to
1 -
HTTP
1 -
https
1 -
Hybrid Cloud
1 -
HyperLogLog
1 -
ike
3 -
import
1 -
Installation & Upgrade
1 -
IoT
1 -
IPSec
4 -
IPSec VPN Administration
1 -
kerberos
1 -
Kubernetes
1 -
Layer 2
1 -
Layer 3
1 -
Learning
1 -
licenses
1 -
local user
3 -
Log Cluster Design
1 -
Log Collection
3 -
Log Collector Design
2 -
Log Management
1 -
Logging
1 -
login
1 -
Logs
3 -
Management
8 -
Management & Administration
5 -
MFA
1 -
Microsoft
1 -
Microsoft 365
1 -
Migration
1 -
minemeld
4 -
multi factor authentication
1 -
multi-factor authentication
1 -
multi-vsys
1 -
NAT
1 -
NetSec
1 -
NetSec Newsletter
1 -
Network Security
35 -
Network Security Management
1 -
Network-Security
1 -
Networking
1 -
newsletter
2 -
Next Generation Firewall
4 -
Next-Generation Firewall
42 -
next-generation firewall. network security
1 -
Next-Generation Firewall. NGFW
6 -
NGFW
31 -
NGFW Configuration
12 -
NGFW Newsletter
1 -
Nominated Discussion
1 -
Objects
2 -
OTP
1 -
PA-3200 Series
1 -
PA-400
1 -
pa-440
2 -
PA-5400 series
1 -
PA-800 Series
1 -
pa-820 firewall
1 -
Packet Buffer
1 -
packet debug
1 -
packet diag
1 -
PAN-OS
17 -
PAN-OS 10.2
1 -
PAN-OS 11.0
1 -
PAN-OS Prisma Access
1 -
Panorama
12 -
Panorama Configuration
2 -
PBF
1 -
PCNSA
1 -
PCNSE
1 -
performance
2 -
policies
2 -
policy
3 -
Policy Based Forwarding
1 -
Prisma Access
7 -
Prisma AIRS
1 -
Prisma SASE
2 -
Prisma SD-WAN
1 -
proactive insights
2 -
Prompt Poaching
1 -
Public Cloud
1 -
Python
2 -
Radius
1 -
Ransomware
1 -
RBI
2 -
region
1 -
Registration
1 -
Remote Browser Isolation
3 -
Reporting
1 -
reporting and logging
1 -
RestAPI
1 -
Risk Management
1 -
Routing
1 -
SAML
1 -
SASE
1 -
script
2 -
SD WAN
1 -
SDWAN
1 -
Search
1 -
Security Advisory
1 -
Security automation
1 -
security policy
4 -
security profile
1 -
Security Profiles
2 -
Selective Push
1 -
Session Packet
1 -
Setup & Administration
8 -
Site-to-Site VPN
1 -
Software Firewalls
1 -
Split Tunneling
2 -
SSL
1 -
SSL Decryption
2 -
SSL Forward Proxy
1 -
SSO
1 -
Strata Cloud Manager
1 -
Strata Logging Service
2 -
Strata Logging Service (SLS)
1 -
Support Guidance
1 -
syslog
1 -
system modes
1 -
Tag
2 -
tags
2 -
Terraform
3 -
Threat
1 -
threat log
1 -
Threat Prevention
1 -
Threat Prevention License
1 -
Tips & Tricks
1 -
TLS
1 -
traffic_log
1 -
Traps
1 -
Troubleshoot
2 -
Troubleshoot. logs
1 -
Troubleshooting
7 -
tunnel
2 -
Tutorial
2 -
Unified Monitoring
1 -
Upgrade
1 -
upgrade-downgrade
2 -
url categories
1 -
URL Filtering
2 -
URL-Filtering
1 -
User ID Probing
1 -
User-ID
1 -
User-ID & Authentication
1 -
User-ID mapping
1 -
userid
1 -
VM Series
1 -
VM-Series
8 -
VM-Series on AWS
3 -
VM-Series on GCP
2 -
VPC Flow logs
1 -
VPN
3 -
VPNs
4 -
Vulnerability
2 -
Vulnerability Protection
1 -
WhatsApp
1 -
WildFire
2 -
Wildfire License
1 -
wmi
1 -
XDR
1 -
xml
2 -
XML API
2
- Previous
- Next





