- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Dynamic update for trial license
- LIVEcommunity
- Discussions
- General Topics
- Dynamic update for trial license
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Dynamic update for trial license
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 03:51 AM
Hi all,
I received PA-200 that was stored on storage for years. The box was unopend so I registered device and requested trial license (according to the portal site, it seemd that the device only had expired Software Warranty Support). After executing "Retrieve license keys from license server", it seemd that the trial license was properly applied to the device and I confirmed updates on PAN-DB via System Log on dashboard.
But regarding to "Application and Threat", no updates took place. In "Dynamic Update" tab, even if I clicked "Check Now", "Last Checked" remains "never". Checking the update on CLI also returns no updates. The PanOS version is 7.0.19 and need updates on Application to update to 7.1.x.
Is it impossible to receive updates on Application and Threat (and Anti-virus) using trial license? Or did I miss something?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 04:05 AM
Hi,
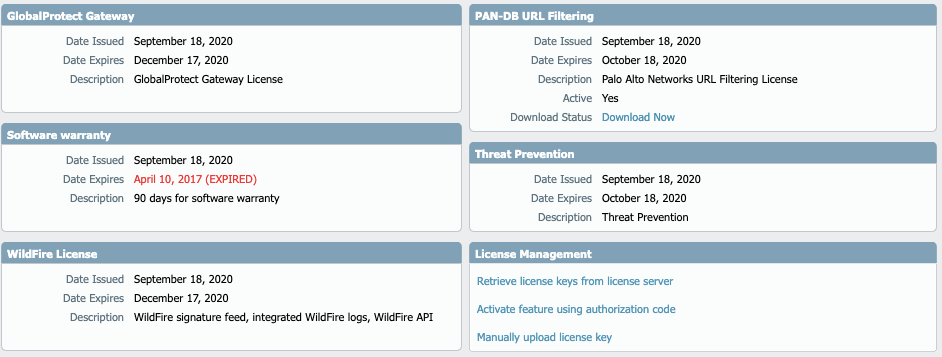
well there are several different trial licences. So basically if you navigate to Device > Licences you should find the PANDB URL Filtering Licence very much alone. If possible please post a screenshot of this page.
René
// If you like my answer force commit it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 04:49 AM
Hi,
Thank you for your prompt reply. Below is the screenshot of "Device" - "License" for PA-200 in question.
I requested all the trial licenses that were available (= except for SD-WAN, IoT and DNS).
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 05:35 AM - edited 09-19-2020 05:38 AM
Hi,
I just did check that on my end. When I initiated a content update. (HA setup in my case)
> request content upgrade download latest sync-to-peer yes
Download job enqueued with jobid 1459
Enqueued Dequeued ID PositionInQ Type Status Result Completed
------------------------------------------------------------------------------------------------------------------------------------------
2020/09/19 14:25:36 14:25:36 1459 Downld FIN OK 14:25:38
First I checked the licences:
> request license info
> request license fetch
If this shows correctly but still doenst work you can disable and reenable the licence:
> request license deactivate key features Threat_Prevention_xx_xx_xx_xxxxxx.key
> request license fetch
Also check if you find something here.
> less mp-log upgradelog_err_content
And check the backend again (palo alto support server) if the licence show up correctly.
Another workaround could be to download the licence.key and manual upload it to the firewall. This process could be tricky sometimes.
Hope that helps.
René
// If you like my answer force commit it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 07:29 AM
> request content upgrade download latest sync-to-peer yes
Server error : No update information available
This looks odd... But it seems that this message is returned by legitimate update server.
My update server in "Device" - "Setup" - "Services" is updates.paloaltonetworks.com.
admin@PA-200> request license info
Current GMT Date: September 19, 2020
(snip)
License entry:
Feature: Threat Prevention
Description: Threat Prevention
Serial: 001606070299
Issued: September 18, 2020
Expires: October 18, 2020
Expired?: no
It seems that there is no problem. request license fetch returns the same result.
admin@PA-200> request license deactivate key features Threat_Prevention_2020_09_18_I5434152.key mode auto
001606070299 Threat Prevention Success
Successfully removed license keys
Done normally. After applying test license again,
admin@PA-200> request license fetch
(snip)
License entry:
Feature: Threat Prevention
Description: Threat Prevention
Serial: 001606070299
Issued: September 19, 2020
Expires: October 19, 2020
Expired?: no
The license is exetended for a day!, but still no change on Dynamic Update page.
I couldn't find upgradelog_err_content log file in my PA-200. Instead, there were following files:
admin@PA-200> less mp-log
agent appweb3-l3svc.log appweb3-panmodule.log appweb3-sslvpn.log appweb3-websrvr.log
authd.log brdagent.log chasd.log cryptod.log dagger.log
devsrv.log dnsproxyd.log dp-monitor.log dsms-certificates.log ehmon.log
ha_agent.log ikemgr.log indexgen.log keymgr.log l2ctrld.log
logpurger.log logrcvr.log masterd.log masterd_apps.log masterd_detail.log
mgmt_fb.log mprelay.log ms.log nf_conntrack.log pan_comm_0.log
pan_dha.log pan_dhcpd.log pan_download.log pan_mgmt_firstboot.log pan_task_1.log
panio.log panlogs-partition.log pdtrc.log php.debug.log php.janitor.log
pppoed.log rasmgr.log reboot.log routed.log satd.log
snmpd.log sslmgr.log stats_service.log supervisor.log sysd.log
sysdagent.log syslog-ng.log useridd.log varrcvr.log vif.log
wildfire-upload.log mp-monitor.log
This might be because my PA-200 runs very old PanOS...
I'll try manual license key upload tomorrow.
Thank you for your kind comment !
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2020 09:04 PM
On older releases (not sure if you mentioned which release you are actually running) it wasn't uncommon to have to install the initial package before you could actually update through dynamic updates. Manually download each dynamic update from the support portal and manually install them on your device; once installed, you should be able to schedule the dynamic updates properly and have it actually function.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-20-2020 09:37 PM
Just now, as a result, the I solved the problem. Though the road to solution was bit weird with back and force.
1. Applied latest Application and Threat Dynamic Update by downloading a file from support site, upload and install via GUI.
2. Application seemed to have failed because autocommit failed repeatedly, but the version on GUI dashboard was updated to the latest version.
3. After the autocommit error stopped, upload PANOS 7.1.0 (running version was 7.0.9) and start update on GUI. Ended with error message "Error: Upgrading from 7.0.1 to 7.1.0 requires a content version of 564 or greater and found 497-2688". It seemd that the applied latest Content wasn't recognized properly.
4. I restarted PANOS because I thought this could fix autocommit error, but autocommit error occured again and to make the matter worse, all NIC but management port became offline.
5. Because downgrade the Content to 497-266 on GUI was failed, I rollbacked the Content on maintenance mode.
6. I seeked the Content file with 3 digits version and finally found panupv2-all-contents-695-4002. Result of application was same as 2 and 3.
7. Same as privious, I rollbacked the Content on maintenance mode but autocommit error and NIC offlien wasn't corrected after restart.
8. I decided to perform factory reset on maintenance mode. The target version was PANOS 7.0.9 which I installed (the openbox version was 6.x.x).
9. After the factory reset, I thought that the Content version would be rollbaced to 497-266, but it was 695-4002. After the reset, "Device" - "Software" returned "No support" and there was no "Install From File". Dynamic Update was same as previous (returns nothing after "Check Now").
10. I downloaded PANOS 7.1.0 from support site and uploaded to PA-200 using "Upload" on GUI.
11. Because there was no "Install From File" in GUI, I logined via CLI and executed "request system software install version 7.1.0"
12. The update was succeeded without problem and PANOS was updated to 7.1.0 after restart. "Application and Threat" and "Wildfire" finally appeared on Dyanmic Update GUI.
In my opinion, what was important was that the latest Content update (and Wildfire as well) wasn't properly recognized by PANOS 7.0.9. I suspect that the PANOS 7.0.9 was too old to correctly recognize the latest Content. It seems that beyond PANOS 7.1.0 recognizes latest Content, but Content update higher than 564 is required to update from 7.0.9. As far as I know, there is no official way to get years-old Content update...
Now that I successfully updated to PANOS 7.1.0 and it seems that Dynamic Update is properly working, I close this topic. If I meet further trouble, I'll create new one. Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-22-2020 01:44 PM
Good job.
René
// If you like my answer force commit it.
- 8146 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- I have a question CVE-2026-0256 PAN-OS in VM-Series in the Public Cloud
- Intergrations of External Dynamic Lists (EDL) with External Systems in Next-Generation Firewall Discussions
- Can you configure clientless VPN in SCM ? in GlobalProtect Discussions
- Cortex XDR Tenant Auto-Upgrade 3.17 → 5.0: UI mixed theme, AI pages stuck loading, Marketplace/Playbook Catalog empty + ingestion quota warning in Cortex XDR Discussions
- What happens when the premium partner and subscription license expires? in Next-Generation Firewall Discussions