- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Issues with Dual ISP Failover
- LIVEcommunity
- Discussions
- General Topics
- Issues with Dual ISP Failover
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-19-2022 02:48 PM
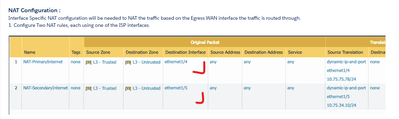
I followed these instructions to set up ISP failover : https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PLL8CAO
When the primary ISP1 goes down, it does indeed fail over to secondary ISP2, in every respect except that traffic doesn't use ISP2's NAT automatically. Upon failover, traffic continues trying to use the NAT rule associated with ISP1. I have to manually go in and DISABLE ISP1's NAT rule, then traffic starts automatically flowing as expected via the NAT rule that exists for ISP2.
What can I do so that this NAT switch happens automatically upon failover?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2022 04:34 AM
Hi @pomologist ,
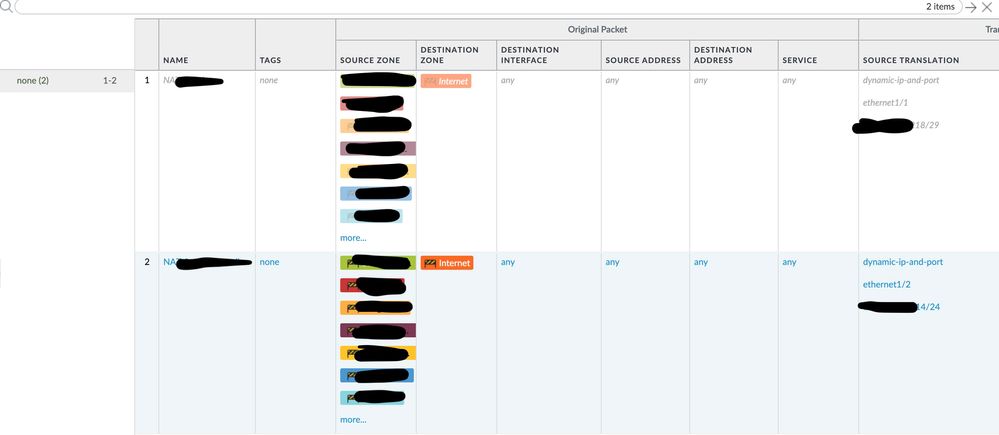
Looking at your screenshot it seems you have missed one key component when configuring the NAT rules - Destination Interface.
NAT rules are evaluated the same way as security rules - first match, top to bottom.
When you configured only source and destination zone for the NAT (using any for source/dest IPs) traffic will always hit the first rule and never reach the second one.
For that reason you must configure "Destination Interface", this will add the egressing interface as part of the matching criteria when evaluating the NAT rules.
So when your primary ISP is up and traffic is using the primary default route your egress/destination interface will be eth1/1 (primary internet).
When primary ISP is down and path monitor "disable" the primary default, traffic will take the backup default, buth this means egress/destination interface will be different, so this traffic will no longer match the first NAT rule and NAT evaluation will keep looking down reaching the second NAT rule.
Hope that make sense
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2022 08:47 AM - edited 08-21-2022 08:49 AM
Update:
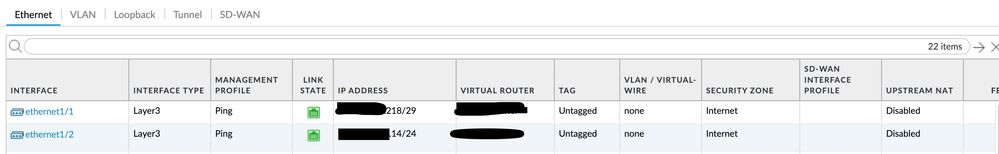
Here are two screenshots that I hope will make things clearer.
Something bizarre is going on. ISP1 uses Eth1/1 Interface. ISP2 uses Eth1/2 interface. Bizarre thing is that Eth1/1 traffic is NATing through Eth 1/2's NAT rule successfully! See photos. What's going on? HELP!
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2022 04:34 AM
Hi @pomologist ,
Looking at your screenshot it seems you have missed one key component when configuring the NAT rules - Destination Interface.
NAT rules are evaluated the same way as security rules - first match, top to bottom.
When you configured only source and destination zone for the NAT (using any for source/dest IPs) traffic will always hit the first rule and never reach the second one.
For that reason you must configure "Destination Interface", this will add the egressing interface as part of the matching criteria when evaluating the NAT rules.
So when your primary ISP is up and traffic is using the primary default route your egress/destination interface will be eth1/1 (primary internet).
When primary ISP is down and path monitor "disable" the primary default, traffic will take the backup default, buth this means egress/destination interface will be different, so this traffic will no longer match the first NAT rule and NAT evaluation will keep looking down reaching the second NAT rule.
Hope that make sense
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2022 06:39 AM
THANK YOU SO MUCH!!! I don't know how I missed that! Yes of course it makes perfect sense. I so much appreciate you pointing this out.
- 1 accepted solution
- 6548 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Conditional Advertisement / BGP Failover with Dual ISP — How to Remove ISP1 Routes on Internet Loss? in Next-Generation Firewall Discussions
- Issue with PA-445 Failover - Interface Reset in General Topics
- Failover is not occurring on the passive device properly. in General Topics