- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Enabling SSO JIT with Microsoft Entra ID (formerly known as Azure Active Directory)
- LIVEcommunity
- Products
- Cloud Native Application Protection
- Prisma Cloud
- Prisma Cloud Articles
- Enabling SSO JIT with Microsoft Entra ID (formerly known as Azure Active Directory)
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 02-13-2024 01:08 PM - edited on 10-29-2024 12:31 PM by RPrasadi
By Irene Garcia, Senior Customer Success Engineer
and
Srikanth Makineni, Customer Success Engineer
Overview
This document provides guidance on how to configure Single Sign On (SSO) between Prisma Cloud Enterprise and Microsoft Entra ID (formally known as Azure Active Directory, or Azure AD) to use Just-in-Time (JIT) provisioning to automatically create users in Prisma Cloud based on their AD Groups assignment.
Steps
- Prisma Cloud Prerequisites (Enabling Direct User Authentication)
- Set up Microsoft Entra ID SSO on Prisma Cloud
- Set up Just-in-Time Provisioning on Microsoft Entra ID
1. Prisma Cloud Prerequisites (Enabling Direct User Authentication)
In Prisma Cloud, go to Settings > Access Control > SSO.
In the section “Direct User Authentication” and select at least one user, who will be able to log in with local credentials in case there is an issue with SSO.
Please Note: If you do not complete this step and SSO does not work, you will need to raise a support case to get SSO disabled in order to log back into the tenant.
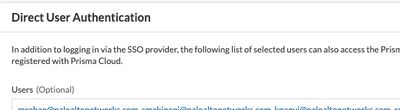
Figure 1: Direct User Authentication_palo-alto-networks
2. Set up Microsoft Entra ID SSO on Prisma Cloud
In Azure:
- Log in to Azure, search/browse to “Microsoft Entra ID”, and click “Enterprise applications”.
- Click “+ New application”.
- Once the application is created, go to the “Single sign-on” page and select “SAML”.
- Scroll down to Step 4 and copy the “Microsoft Entra identifier”.
In Prisma Cloud:
5. Go to “Settings > Access Control > SSO” and select “SAML” protocol and click on “Enabled”:
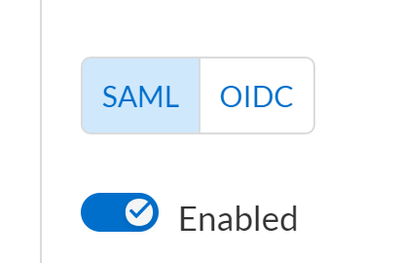
Figure 2: Enable SAML protocol_palo-alto-networks
6. Paste the previous copied URL into the “Identity Provider Issuer” field.
7. Copy the “Audience URI (SP Entity ID)”.
In Azure:
8. In Step 1 (“Basic SAML Configuration”), click “edit” and paste that value in the “Identifier (Entity ID)” field.
9. The “Reply URL (Assertion Consumer Service URL)” field will depend on the location of your tenant, which is displayed in the login URL. You will need to replace “app” with “api” and append “/saml” at the end. For example, for the following login URL:
https://app2.eu.prismacloud.io
The value for this field will be:
https://api2.eu.prismacloud.io/saml
10. In Step 3 (“SAML Signing Certificate”), click “Add a certificate” and then “New Certificate”. Enter an expiration date
and notification email address and click “Save”.
11. Go back to step 3 and download the “Certificate (Base64)”.
In Prisma Cloud:
12. Paste the certificate value (including the “BEGIN” and “END” lines) in the “Certificate” section:
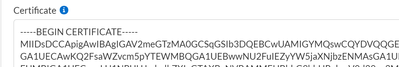
Figure 3: Certificate field_palo-alto-networks
13. Before clicking on “Save”, please validate the following prerequisites are in place:
- In Prisma Cloud, you have at least one user under the “Direct User Authentication” section (just in case the SSO integration does not work)
- The user used for the SSO test:
- Exists in Prisma Cloud under “Settings > Access Control > Users”
- Has an assigned role in Prisma Cloud
- Is assigned to the Microsoft Entra enterprise application in the “Users and Groups” section (either directly or by being a member of an assigned group)
- Click “Save” and test the SSO integration.
3. Set up Just-in-Time Provisioning on Microsoft Entra ID
Once the SSO integration is working, we can proceed to enable JIT. The idea is to automate the process of creating accounts for users. In other words, the user will not be required to be in the “Settings > Access Control > Users” list, instead, it will automatically be added to that list with a role automatically assigned.
The most important part of JIT settings are the values sent as a part of the SAML assertion. Prisma Cloud requires the following fields:
- Email Address
- Role
- First Name
- Last Name
By default, the Microsoft Entra enterprise application previously created will already have three fields: email address, first name, and last name. On the other hand, we will create a new attribute for the “role” field. In that case, the value sent from Azure has to map to an existing role in Prisma Cloud. If any of the required attributes don’t exist, the JIT SSO login will fail.
In Azure:
- Go to the SSO Enterprise Application that you configured in the previous section. Click on “Single sign-on” and on “Edit” in the section 2: “User Attributes & Claims”
- Click on “Add a group claim”:
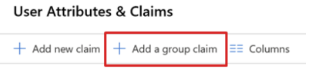
Figure 4: Add a group claim_palo-alto-networks
- Select “Groups assigned to the application”, “sAMAccountName” as “Source attribute”
and customize the name of the group claim:

Figure 5: Group claim configuration_palo-alto-networks
After that, the “Attributes & claims” view should look like this:

Figure 6: Attributes & Claims configuration_palo-alto-networks
In Prisma Cloud:
- Go to “Settings > Access Control > SSO” and click on “Enabled” in the “Just in Time (JIT) Provisioning” section.
- Update the fields with the corresponding Microsoft Entra ID claim names. With the previous Microsoft Entra ID “Attributes & Claims” view, the Prisma Cloud configuration should look like this:

Figure 7: Prisma Cloud JIT configuration_palo-alto-networks
- Click on “Save”.
- Go to “Settings > Access Control > Roles” and create as many roles as desired. The role names should exactly match the Microsoft Entra ID group names assigned to the Microsoft Entra enterprise application.
- Before testing the JIT integration, please validate the following prerequisites are in place:
- The user used for the SSO JIT test:
- Does not exist in Prisma Cloud under “Settings > Access Control > Users” (just to confirm that it is automatically added to the list after a successful JIT test).
- Is a member of at least one of the Microsoft Entra ID groups assigned to the Microsoft Entra enterprise application.
- The same groups you have in Microsoft Entra ID also exist with the exact same name in Prisma Cloud as roles. This configuration relies on assigning a role called exactly the same way as the attribute coming in the SAML response. For example, the roles could have these names in Prisma Cloud:

Figure 8: Prisma Cloud Roles_palo-alto-networks
And in that case, the Groups assigned to the Microsoft Entra enterprise application must have the same names:

Figure 9: Microsoft Entra enterprise application Users and Groups_palo-alto-networks
With this configuration, whenever a user is a member of one or multiple Microsoft Entra ID groups whose name is a Prisma Cloud role, the user will have that role(s) assigned.
Once the configuration is working, you will need to do the following in case you would like to have more roles assigned to users. Let's say you would like user "XX" to have the role "YY":
- In Azure, validate the user "XX" is a member of the group "YY"
- In Azure, in the Prisma Cloud Enterprise Application, assign the group "YY" in the section "Users and groups"
- In Prisma Cloud, create a role with the name "YY"
Conclusion
Enabling and controlling access to IT resources and applications is an important aspect of securing an organization. An identity provider such as Microsoft Entra ID is used by many organizations, and this article has given you the required information to connect Prisma Cloud with users and roles defined in Microsoft Entra ID by the following three steps:
- Enable Direct User Authentication in Prisma Cloud
- Setup Microsoft Entra SSO on Prisma Cloud
- Microsoft Entra SSO Group Claims Setup Just-in-time Provisioning on Microsoft Entra ID
This then allows users to be automatically created in Prisma Cloud when the user gets access to Prisma Cloud using Microsoft Entra SSO. The user’s role and permissions will be based on the Microsoft Entra Groups assignment. No manual creation of users will be required for your organization’s users to log into Prisma Cloud. As long as the Microsoft Entra ID provides the user with the permissions to access Prisma Cloud, the user will be able to log in with the appropriate credentials with access levels as configured in Microsoft Entra ID.
Reference
Set up Azure AD SSO on Prisma Cloud
About the Authors
- 9711 Views
- 0 comments
- 1 Likes
- Microsoft Azure NSG flow log setup and benefits in Prisma Cloud in Prisma Cloud Articles
- How to Deploy Prisma Cloud App-Embedded Defender in Azure ACI in Prisma Cloud Articles
- Drift detection of IaC templates tracing with yor trace in Azure DevOps in Prisma Cloud Articles
- Protecting Azure AI services with Prisma Cloud AI-SPM in Prisma Cloud Articles
- Azure Onboarding: Alternative Approach in Prisma Cloud Articles
-
Access Control
1 -
Access Key
1 -
ACI
1 -
Action Plans
1 -
Active Directory Groups
1 -
Agentless
2 -
Agentless VM Scanning
1 -
AI
1 -
AI-Driven solution
1 -
AISPM
1 -
Amazon ECS
1 -
Amazon Eventbridge
1 -
API
2 -
App Embeded
1 -
Application Programming Interface
1 -
ApplicationSecurity
1 -
Approach
1 -
Asset inventory
1 -
Asset Inventory Dashboard
1 -
Asset Inventory. AWS EKS
1 -
Assets
1 -
Attack Path
1 -
Attack path vectors
1 -
Audit
1 -
audit stream
1 -
Authentication
1 -
Authorization
1 -
Auto Map
1 -
auto-remediation
2 -
automatic defender install
1 -
AWS
1 -
AWS Account Onboarding
1 -
AWS Cloud Watch
1 -
AWS EC2
1 -
AWS Secrets Manager
1 -
Azure
6 -
Azure Cloud Accounts
1 -
Azure Container Instances
1 -
Azure RBAC
1 -
Azure Sentinel
1 -
Azure Single Sign On (SSO)
1 -
Azure VM Image Scanning
1 -
Beginner to Intermediate Level
5 -
Building Images
1 -
CI
1 -
CICD
1 -
CLI command
2 -
cloud assets
1 -
Cloud Performance monitoring
1 -
Cloud Security
10 -
Cloud Security Posture Management
1 -
Cloud Security Posture Management (CSPM)
6 -
Cloud Workload Protection
1 -
Cloud Workload Protection Platform (CWPP)
4 -
Collection Scoping
1 -
compliance scanning
1 -
Compliance Standard
1 -
Compute
2 -
Compute Edition
4 -
Compute SaaS
1 -
Configuration
1 -
console
1 -
Container Defender
2 -
Container Image
1 -
Containers
2 -
Control Plane
1 -
Cost Optimisation
1 -
cspm
2 -
Custom rules
1 -
CVE
2 -
CWP Token
1 -
CWPP
2 -
DaemonSet
1 -
Daemonsets
1 -
Dashboards
1 -
Defender
2 -
Defender Deployment
5 -
Defender Upgrade
1 -
devops
1 -
DevSecOps
1 -
DevSecOps ShiftLeft
2 -
DevTools
1 -
docker swarm
1 -
EKS logs
1 -
Event Assisted Ingestion
1 -
Eventbridge
1 -
Events
1 -
FinOps
1 -
FN
1 -
FP
1 -
GCP Organization Onboarding
1 -
General Articles
2 -
GitHub
2 -
GitOps
1 -
GKE
1 -
Google Security Operations
1 -
Helm Charts
1 -
host auto defend
1 -
Host Defender
1 -
host vulnerabilities
2 -
Hosts
1 -
Hub account
1 -
IAC
1 -
IAM
1 -
IAM misconfigurations
1 -
Identity federation.
1 -
Image Scanning
1 -
Ingress
1 -
install defender
1 -
Integration
2 -
Intermediate Skill Level
2 -
Jenkins
1 -
Jfrog Artifactory
1 -
Jira
1 -
Jira Tickets
1 -
JIT
1 -
JWT
1 -
JWT Token
1 -
Kubernetes
7 -
Kubernetes auditing
1 -
Kubernetes Clusters
1 -
lateral movement
1 -
Layer
1 -
Least Privilege
1 -
Least privilege Principle
1 -
Log4j
1 -
MFA (Multi-Factor Authentication)
1 -
Microsoft Azure subscriptions
1 -
Microsoft Entra.
1 -
Nested Account Groups
1 -
Network
1 -
Network Anomaly
1 -
Network Exposure
1 -
NGINX
1 -
NSG Flow Logs
1 -
NVD
1 -
Onboarding
2 -
Onebox
1 -
Organizing Cloud Resources
1 -
PAM (Privileged Access Management)
1 -
PCEE
1 -
playbooks
2 -
Plug in
1 -
Postman
1 -
prioritize risk
4 -
Prisma "cloud code security" (CCS) module
1 -
Prisma Cloud
29 -
Prisma Cloud Asset Inventory Dashboard
1 -
Prisma Cloud Code Security
1 -
Prisma Cloud Compute
6 -
Prisma Cloud Compute Edition
7 -
Prisma Cloud Compute Edition Administrator’s Guide
1 -
Prisma Cloud Enterprise Edition
2 -
Prisma Cloud Intelligence Stream(IS)
3 -
Prisma Cloud Intelligence Stream(IS) feed
2 -
Prisma Cloud SaaS API
1 -
Prisma Cloud Terraform Provider
1 -
PrismaCloud
1 -
privilege escalation
1 -
protect your EC2
1 -
Radar
1 -
RBAC (Role-Based Access Control)
1 -
Recursive Hierarchy
1 -
reference “Prisma Cloud Administrator’s Guide”
1 -
reference “Prisma Cloud Compute Edition Administrator’s Guide”
2 -
Risk Prioritization
1 -
RQL
1 -
Runtime Security
3 -
SDLC
1 -
Secrets
2 -
SecureDevelopment
1 -
Security
2 -
Security Posture
1 -
security-relevant events
1 -
Serverless
1 -
Service Account
1 -
shift left
1 -
Shift-Left
1 -
SIEM
1 -
SSO (Single Sign-On)
1 -
TCP Handshake
1 -
TCPIP
1 -
Terraform
1 -
thread feed
4 -
threat intelligence
4 -
TLS Handshake
1 -
Token
1 -
Visibility
1 -
VM
1 -
VM Scanning
1 -
VSCode
1 -
vulnerabilities
1 -
Vulnerability
1 -
vulnerability detection
7 -
Vulnerability Management
7 -
Vulnerability Protection
1 -
WAAS
1 -
Webshell
1 -
Windows
2 -
XSOAR
2 -
Yor
1




