- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
mapping issue
- LIVEcommunity
- Discussions
- General Topics
- mapping issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 04:35 AM
Good Day to everyone.
I have this issue almost every day. It doesn't happen with all users at one time.
After restart, everything is working as it should work.
I have probe enabled(20 minutes) and Enable User Identification Timeout(720 minutes).
What can be an issue?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-20-2018 03:00 AM
you can use CP and GP in vwire - but indeed this needs some more further configuration steps - to much to handle it in his issue.
But you can find a lot of useful documents in the PaloAlto Knowledgebase, e.g. this one for CP: https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClJYCA0
Regarding GP and internal gateways there are several articles around here and you can also find the info in the admin guide.
Regarding UIA instances: you can install the User-ID Agent on Windows servers in your environment, please take a look at documentation. At the moment its seems you only use the agent on the firewall itself.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 06:17 AM
And a very good day to you kind sir...
are you using agents or local palo user mapping.
what is it that you restart to get things working again. the firewall, user PC... or all
it dose seem odd as you have the timeout set to 12 hours....
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 10:10 AM
Hi Mick,
I restart pc which has this problem and after restart everything is working.
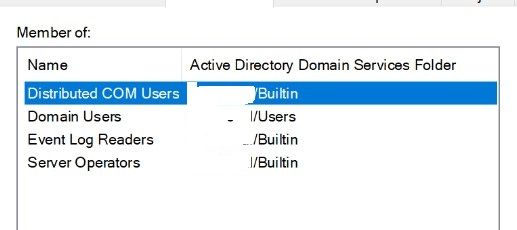
I use AD username to make connection between PAN and AD.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 11:22 AM
So how long after you restart the pc does the problem come back for that user.. Is it after 12 hours.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 09:57 PM - edited 11-14-2018 09:57 PM
For other users it happens at different time, so I can't tell you exact time.
But with me it happens almost every morning. I take my pc home at 6 PM and come at work at 9 AM.
It makes about 15 hours.
Also if some user turns off his pc for this time and turns it on in the morning the same problem occurs.
I now made this time for 20 hours. Maybe you have another solution?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2018 10:51 PM
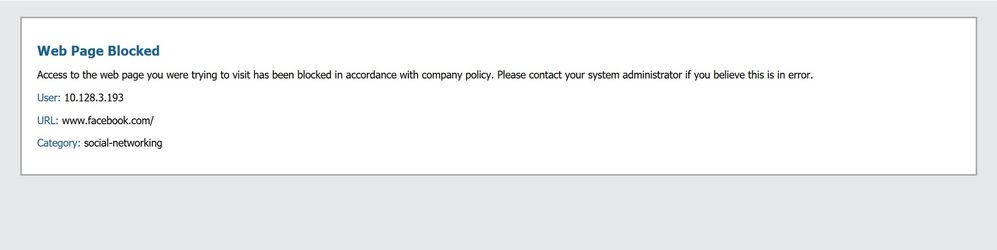
Also it does the problem when I switch to WIFI network.
It blocks by ip.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 12:35 AM
It looks like you rely on AD security log for user-id and your probing configuration does not work.
So when you login via cable the firewall/UIA learns the mapping from the AD security log, but when you switch network connection I think you get a new IP. As there is no login event on the AD you have no correct user-ip-mapping and the connection is blocked.
Did you set the correct permissions for probing?
Take a look at: https://live.paloaltonetworks.com/t5/General-Topics/Permissions-of-user-ID-service-account-for-wmi-a...
You can check wether your AD account is allowed to get the logged in user via the following cli command on windows:
WMIC /NODE: xxx.xxx.xxx.xxx COMPUTERSYSTEM GET USERNAME
Make sure that you run that command in the context of your UID Agent user!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 02:12 AM
Hi ALex,
probing and etc is configured as in this article.
I just added now our local DATA network in include/exclude network (include - 10.0.0.0/8).
The problem usually occurs on mornings.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 04:46 AM
the article you mentioned does not cover the permission settings on windows side.
Please use the wmic command mentioned before to test if you receive the userinformation from the client. when you receive an empty response, the permissions are not correct
The network for sure must be in the include list for the firewall to create a ip-user-mapping.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-15-2018 09:55 AM
Hello,
Do you use MS exchange for email? If yes, I have found those logs to be quicker to respond to IP changes, i.e. wireless to WiFi. Sometime what happens on a PC is that other accounts are running on it from external sources so the mapping in the PAN wont be correct.
For example if you use a 3rd party tool to push out software or updates that uses a service account, then the IP to User maping in the PAN will most likly show the service account since it only uses the last account to log into a PC.
This has caused me issues in the past when performing vulnerability scans. All of a sudden it would look like my scanning account was logged into the PC, and it was, for scanning purposes.
You can check the Unified logs to make sure the IP/Username is correct for that PC or help you track down what is causing it to change.
Hope that helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2018 04:44 AM
Alex, we gave this permissions to integrated user. I issued command you said and it's working.
But when I change to wifi it doesn't work for some time. I have to restart or wait for 10-15 minutes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2018 04:55 AM
Hi Otakar!
I checked in Unified logs when I changed to wifi and mapping didn't happen, but there were no logs.
And yes we user Exchange server. Should there be any config change or?
Can you post some link or anything.
Thanks in advance!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2018 06:43 AM
Did you test from the user-id agent or on the local computer?
When you establish a connection and the ip is unknown this should trigger the probing. Depending on your network you may be blocking the probing on the firewall? Also wmi is quite slow, so check the logs of the UIA if there are a lot of probes pending/queued.
Regarding Exchange server, you can use this as source for user-information too on the UIA - usually you get more user login events on that system. But this would also require that your Exchange is reachable without user information.
When it goes to service-users for software deployment or scans: put those users in the exclude list!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2018 07:55 AM
Hello,
Yes if you want to monitor the exchange logs, you will need to perform reconfiguration of the user-id setup.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClGGCA0
Instead of Microsoft ACtive directory, use Microsoft Exchange.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-19-2018 02:56 AM
I test both from local computer and the user-id agent.
Probing is set for 20 minutes(default). I'll check logs the next time this issue will occur.
Maybe there any alternative to wmi if it's so slow?
Regardless Exchange server config: we have some users, me for example, which has 2-3 mail accounts. This are different people accounts, which leave the work and we need them. Their accounts are disabled, but mail accounts are working. It'll also create an issue I think.
- 1 accepted solution
- 12314 Views
- 18 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- PA-410 commit shows internal error and found that logdb-quota shows abnormal in General Topics
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions