- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
syslog udp session keep alive ?
- LIVEcommunity
- Discussions
- General Topics
- syslog udp session keep alive ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
syslog udp session keep alive ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-28-2022 09:38 PM
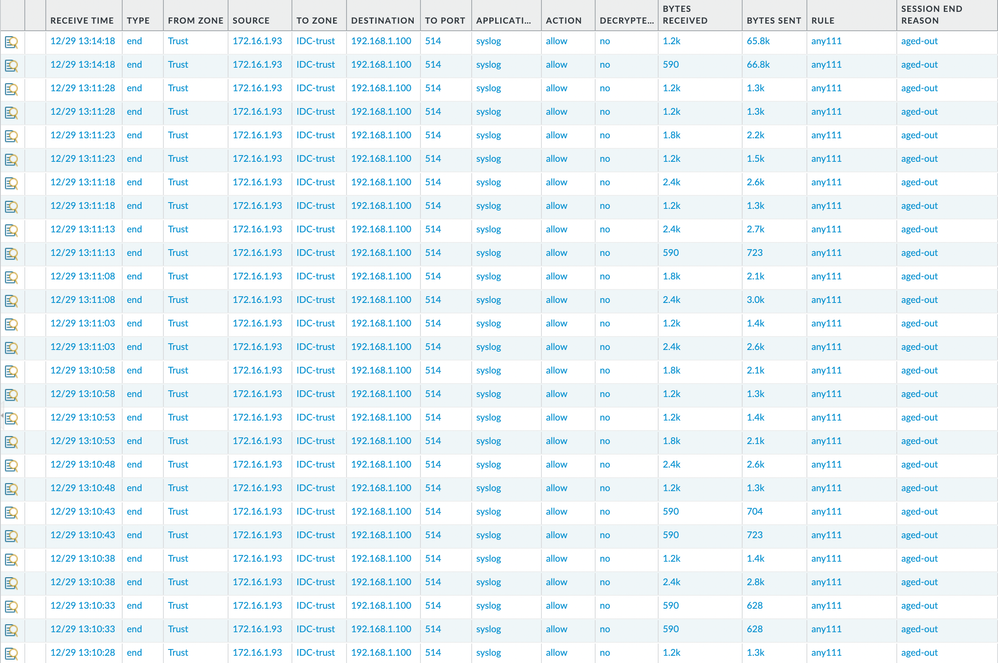
When forwarding logs, they are being sent to udp 514. The udp time out is 30 seconds, and the syslog server actually receives packets every 5 seconds. However, I wonder why the firewall keeps the session longer than 30 seconds. When the time is long, it is several minutes or hours, and sometimes the date passes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-29-2022 01:09 PM
Hello,
Its because they are UDP packets/sessions. Here is an article from Palo Alto on this:
When monitoring the traffic logs using Monitor > logs > Traffic, some traffic is seen with the Session End Reason as aged-out. Any traffic that uses UDP or ICMP is seen will have session end reason as aged-out in the traffic log. This is because unlike TCP, there is there is no way for a graceful termination of UDP session and so aged-out is a legitimate session-end reason for UDP (and ICMP) sessions.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMjLCAW
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2022 08:51 AM
If you add "From port", "Packets sent" and "Packets received" columns you can see that until syslog sender is sending traffic from same source port Palo keeps same session open and packets are gathered under same session.
If no new packets in this session for 30 seconds then this session is closed.
Palo Alto Networks certified from 2011
- 3602 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- PA440 HA failover not working in General Topics
- After software upgrade firewall stopped to sending syslog in General Topics
- DNS Failover Service in Next-Generation Firewall Discussions
- Firewall SSH, the login succeeds with TACACS Account, but there is an issue that closes the session immediately. in Next-Generation Firewall Discussions