- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
URL Filtering For Inbound Servers
- LIVEcommunity
- Discussions
- General Topics
- URL Filtering For Inbound Servers
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
URL Filtering For Inbound Servers
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2022 12:21 AM - edited 03-23-2022 12:36 AM
Hi Team,
will it actually make sense to apply the URL Filtering for the Inbound traffic to our Internal Server?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2022 07:12 AM
Hi @SubaMuthuram ,
I see one use-case where you could apply URL filtering to restrict the incoming URL to something specific ... in order to prevent folder hopping or directory searching.
Cheers,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2022 05:37 PM
There's some very specific scenarios where it can be useful in certain edge cases, but it's not generally something that I would worry about. Generally speaking creating custom App-IDs, and where needed vulnerability signatures for something like ECP in an on-prem Exchange environment, is more useful for the vast majority of environments.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2022 04:20 AM
Hi Team,
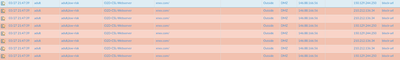
Thanks for the reply, One of our client has the below issue, Whenever they trying to access their internal server from outside, in the URL filtering the traffic is categorized as Adult category and the URL showing xnxx.com
Please refer the below image,
Please enlighten me what is the logic behind this, Is it indicating the traffic from malicious IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2022 04:42 AM
in the URL the customer is using, does it contain xnxx.com in any way? you may need to disable "log container pages only" in the url filtering profile to see this information
you could try the following:
create a custom url category containing the right URLs for the internal webserver
set the custom category in the services/url tab of the security rule
remove the url filtering profile from the security profiles
PANgurus - Strata & Prisma Access specialist
- 6618 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- Header Fields for Syslog for Rapid7 in Next-Generation Firewall Discussions
- NPN Incident - Suggest a "software repository" URL Category? in Next-Generation Firewall Discussions
- Website Filtering Dillema in General Topics
- IP address being blocked by PAN Malicious IP Feeds Inbound on PA820 in Next-Generation Firewall Discussions